WordPress security is a critical concern for all website owners. With thousands of websites being blacklisted every day for malware and phishing, it's essential to implement the best practices for securing your WordPress blog. This guide will provide you with actionable steps and insights into WordPress security, including the importance of keeping WordPress updated, using strong passwords, and the role of web hosting in protecting your site.
Key Takeaways
Why WordPress Security is Important
The security of your WordPress site is of utmost importance in order to protect your website from hackers and prevent malware attacks. Security breaches can lead to data theft, the distribution of harmful malware, and even ransomware attacks. Not only can these breaches cause significant damage to your website and reputation, but they can also result in legal and financial consequences for your business.
In addition to protecting your own information, it is essential to consider your visitors' expectations. Internet users today are increasingly aware of the importance of online security, and they expect websites to provide a safe browsing experience. A secure website builds trust and credibility with your audience, increasing the likelihood of return visits and conversions. Furthermore, search engines like Google prioritize secure sites in their rankings, meaning that investing in WordPress security measures can also improve your website's visibility and organic traffic.
Protect Your Website from Hackers and Malware
By implementing proper WordPress security measures, you can safeguard your website and protect it from potential threats. This includes regularly updating WordPress, plugins, and themes, as updates often include security patches that address vulnerabilities. It also involves using strong passwords for your admin accounts, limiting login attempts, and enabling two-factor authentication to prevent unauthorized access.
Another key aspect of WordPress security is choosing a reliable web hosting provider. A secure hosting environment ensures that your website is hosted on servers that are protected against common threats and regularly updated with the latest security measures. Managed WordPress hosting, in particular, offers enhanced security features such as automatic backups, regular software updates, and advanced security configurations, providing an additional layer of protection for your site.
| Benefits of WordPress Security | Measures to Protect Your Website |
| 1. Protection against data theft and malware distribution | 1. Regularly update WordPress, plugins, and themes |
| 2. Enhanced trust and credibility with your audience | 2. Use strong passwords and limit login attempts |
| 3. Improved search engine visibility and organic traffic | 3. Enable two-factor authentication |
| 4. Legal and financial consequences | 4. Choose a reliable web hosting provider |
Keeping WordPress Updated
Regularly updating your WordPress installation, plugins, and themes is essential for maintaining a secure website. Updates often include security patches that address vulnerabilities and protect against potential threats. By keeping your WordPress site up to date, you minimize the risk of hacking attempts and ensure the stability of your site.
Updating WordPress is a straightforward process. Once a new version is released, you'll receive a notification in your WordPress dashboard. Simply click on the update button to initiate the update. It's important to back up your site before performing any updates to avoid any potential data loss. Additionally, it's crucial to update your plugins and themes as well. Outdated versions can expose your site to security risks.
To update your plugins, go to the "Plugins" section in your WordPress dashboard. If an update is available, you'll see a notification next to the plugin name. Click on the "Update Now" button to update the plugin. Similarly, for themes, navigate to the "Appearance" section and click on the "Themes" tab. If an update is available for your active theme, you'll see an update notification. Click on the "Update Now" button to update the theme.
| Key Actions | Purpose |
| Regularly update WordPress, plugins, and themes | Address vulnerabilities and protect against potential threats |
| Back up your site before performing updates | Minimize the risk of data loss |
| Update plugins in the "Plugins" section | Ensure plugins are up to date |
| Update themes in the "Appearance" section | Keep your active theme secure |
By prioritizing regular updates, you can strengthen the security of your WordPress site and stay protected against emerging threats.
Passwords and User Permissions
Creating strong passwords and managing user permissions are vital aspects of WordPress security. By implementing best practices in password management and user access control, you can significantly enhance the security of your WordPress site and protect it from unauthorized access.
Strong Passwords
Using strong, unique passwords is essential to prevent unauthorized access to your WordPress site. Avoid using commonly used passwords or personal information that can be easily guessed. Instead, create passwords with a combination of uppercase and lowercase letters, numbers, and special characters. Regularly updating passwords is also recommended to mitigate any potential risks.
Limit Login Attempts
Limiting the number of login attempts can deter hackers from using brute force attacks to gain access to your WordPress site. By setting a limit on the number of failed login attempts, you can effectively block repeated login attempts, making it more difficult for unauthorized users to guess or crack your password.
Two-Factor Authentication
Implementing two-factor authentication adds an extra layer of security to your WordPress login process. This authentication method requires users to provide an additional verification code, usually sent to their mobile device, after entering their password. By enabling two-factor authentication, you can ensure that only authorized individuals with both the password and the verification code can access your WordPress site.
Password Protect wp-admin and Login Pages
Another important security measure is to password protect the wp-admin directory and the login pages of your WordPress site. This additional layer of protection prevents unauthorized access to sensitive areas of your site, such as the WordPress admin panel. Password protecting these pages adds an extra barrier for potential hackers, making it more challenging for them to gain control of your WordPress site.
Table: User Permissions
| User Role | Capabilities |
| Administrator | Full access to all WordPress settings and functionality |
| Editor | Can create, edit, publish, and delete all posts and pages |
| Author | Can create, edit, publish, and delete their own posts |
| Contributor | Can write and edit their own drafts, but cannot publish them |
| Subscriber | Can only manage their profile and leave comments on your site |
Understanding user roles and permissions is crucial for controlling access to your WordPress site. By assigning appropriate user roles to individuals, you can limit their capabilities and ensure that only trusted users have access to critical administrative functions. Regularly review and update user permissions to maintain the security of your WordPress site.
The Role of Web Hosting
When it comes to securing your WordPress site, the choice of web hosting provider is crucial. A reliable and secure web hosting provider plays a significant role in protecting your website from potential threats. With web hosting security being a top priority, it's essential to choose a provider that offers advanced security features and robust infrastructure.
Managed WordPress hosting is an excellent option for ensuring the security of your WordPress site. By opting for managed hosting, you can benefit from automatic backups, regular updates, and enhanced security configurations. These features can significantly reduce the risk of security breaches and provide peace of mind.
The Benefits of Managed WordPress Hosting
Managed WordPress hosting offers several advantages when it comes to website security:
By choosing a secure web hosting provider, such as a reputable managed WordPress hosting service, you can enhance the security of your WordPress site and protect it from potential threats.
Conclusion
Securing your WordPress blog with hosting is of utmost importance to protect your website from hackers and malware. By implementing the best practices outlined in this guide, you can significantly enhance the security of your WordPress site and ensure a safe online presence.
Remember that WordPress security is an ongoing process, and it requires active vigilance. Keep your WordPress installation, plugins, and themes up to date to stay protected against potential threats. Additionally, use strong and unique passwords for your admin, FTP, and hosting accounts. Consider implementing measures like limiting login attempts and enabling two-factor authentication to further enhance your site's security.
Choosing a secure web hosting provider is also crucial. Opt for a reputable company that takes proactive measures to protect their servers and offers advanced security configurations. Managed WordPress hosting can provide automatic backups, regular updates, and enhanced security features to ensure the safety of your website. Prioritize the security of your WordPress site by selecting a web hosting provider with a proven track record in WordPress security.
By following these WordPress security best practices and investing in secure WordPress hosting, you can protect your website from hackers, safeguard your data, and maintain the trust of your visitors. Don't compromise on the importance of WordPress security - prioritize the security of your WordPress blog today for a secure and successful online presence.
Create an image featuring a shield or barrier with a WordPress logo inside, representing the idea of secure hosting.
Key Takeaways
Why WordPress Security is Important
The security of your WordPress site is of utmost importance in order to protect your website from hackers and prevent malware attacks. Security breaches can lead to data theft, the distribution of harmful malware, and even ransomware attacks. Not only can these breaches cause significant damage to your website and reputation, but they can also result in legal and financial consequences for your business.
In addition to protecting your own information, it is essential to consider your visitors' expectations. Internet users today are increasingly aware of the importance of online security, and they expect websites to provide a safe browsing experience. A secure website builds trust and credibility with your audience, increasing the likelihood of return visits and conversions. Furthermore, search engines like Google prioritize secure sites in their rankings, meaning that investing in WordPress security measures can also improve your website's visibility and organic traffic.
Protect Your Website from Hackers and Malware
By implementing proper WordPress security measures, you can safeguard your website and protect it from potential threats. This includes regularly updating WordPress, plugins, and themes, as updates often include security patches that address vulnerabilities. It also involves using strong passwords for your admin accounts, limiting login attempts, and enabling two-factor authentication to prevent unauthorized access.
Another key aspect of WordPress security is choosing a reliable web hosting provider. A secure hosting environment ensures that your website is hosted on servers that are protected against common threats and regularly updated with the latest security measures. Managed WordPress hosting, in particular, offers enhanced security features such as automatic backups, regular software updates, and advanced security configurations, providing an additional layer of protection for your site.
| Benefits of WordPress Security | Measures to Protect Your Website |
| 1. Protection against data theft and malware distribution | 1. Regularly update WordPress, plugins, and themes |
| 2. Enhanced trust and credibility with your audience | 2. Use strong passwords and limit login attempts |
| 3. Improved search engine visibility and organic traffic | 3. Enable two-factor authentication |
| 4. Legal and financial consequences | 4. Choose a reliable web hosting provider |
Keeping WordPress Updated
Regularly updating your WordPress installation, plugins, and themes is essential for maintaining a secure website. Updates often include security patches that address vulnerabilities and protect against potential threats. By keeping your WordPress site up to date, you minimize the risk of hacking attempts and ensure the stability of your site.
Updating WordPress is a straightforward process. Once a new version is released, you'll receive a notification in your WordPress dashboard. Simply click on the update button to initiate the update. It's important to back up your site before performing any updates to avoid any potential data loss. Additionally, it's crucial to update your plugins and themes as well. Outdated versions can expose your site to security risks.
To update your plugins, go to the "Plugins" section in your WordPress dashboard. If an update is available, you'll see a notification next to the plugin name. Click on the "Update Now" button to update the plugin. Similarly, for themes, navigate to the "Appearance" section and click on the "Themes" tab. If an update is available for your active theme, you'll see an update notification. Click on the "Update Now" button to update the theme.
| Key Actions | Purpose |
| Regularly update WordPress, plugins, and themes | Address vulnerabilities and protect against potential threats |
| Back up your site before performing updates | Minimize the risk of data loss |
| Update plugins in the "Plugins" section | Ensure plugins are up to date |
| Update themes in the "Appearance" section | Keep your active theme secure |
By prioritizing regular updates, you can strengthen the security of your WordPress site and stay protected against emerging threats.
Passwords and User Permissions
Creating strong passwords and managing user permissions are vital aspects of WordPress security. By implementing best practices in password management and user access control, you can significantly enhance the security of your WordPress site and protect it from unauthorized access.
Strong Passwords
Using strong, unique passwords is essential to prevent unauthorized access to your WordPress site. Avoid using commonly used passwords or personal information that can be easily guessed. Instead, create passwords with a combination of uppercase and lowercase letters, numbers, and special characters. Regularly updating passwords is also recommended to mitigate any potential risks.
Limit Login Attempts
Limiting the number of login attempts can deter hackers from using brute force attacks to gain access to your WordPress site. By setting a limit on the number of failed login attempts, you can effectively block repeated login attempts, making it more difficult for unauthorized users to guess or crack your password.
Two-Factor Authentication
Implementing two-factor authentication adds an extra layer of security to your WordPress login process. This authentication method requires users to provide an additional verification code, usually sent to their mobile device, after entering their password. By enabling two-factor authentication, you can ensure that only authorized individuals with both the password and the verification code can access your WordPress site.
Password Protect wp-admin and Login Pages
Another important security measure is to password protect the wp-admin directory and the login pages of your WordPress site. This additional layer of protection prevents unauthorized access to sensitive areas of your site, such as the WordPress admin panel. Password protecting these pages adds an extra barrier for potential hackers, making it more challenging for them to gain control of your WordPress site.
Table: User Permissions
| User Role | Capabilities |
| Administrator | Full access to all WordPress settings and functionality |
| Editor | Can create, edit, publish, and delete all posts and pages |
| Author | Can create, edit, publish, and delete their own posts |
| Contributor | Can write and edit their own drafts, but cannot publish them |
| Subscriber | Can only manage their profile and leave comments on your site |
Understanding user roles and permissions is crucial for controlling access to your WordPress site. By assigning appropriate user roles to individuals, you can limit their capabilities and ensure that only trusted users have access to critical administrative functions. Regularly review and update user permissions to maintain the security of your WordPress site.
The Role of Web Hosting
When it comes to securing your WordPress site, the choice of web hosting provider is crucial. A reliable and secure web hosting provider plays a significant role in protecting your website from potential threats. With web hosting security being a top priority, it's essential to choose a provider that offers advanced security features and robust infrastructure.
Managed WordPress hosting is an excellent option for ensuring the security of your WordPress site. By opting for managed hosting, you can benefit from automatic backups, regular updates, and enhanced security configurations. These features can significantly reduce the risk of security breaches and provide peace of mind.
The Benefits of Managed WordPress Hosting
Managed WordPress hosting offers several advantages when it comes to website security:
By choosing a secure web hosting provider, such as a reputable managed WordPress hosting service, you can enhance the security of your WordPress site and protect it from potential threats.
Conclusion
Securing your WordPress blog with hosting is of utmost importance to protect your website from hackers and malware. By implementing the best practices outlined in this guide, you can significantly enhance the security of your WordPress site and ensure a safe online presence.
Remember that WordPress security is an ongoing process, and it requires active vigilance. Keep your WordPress installation, plugins, and themes up to date to stay protected against potential threats. Additionally, use strong and unique passwords for your admin, FTP, and hosting accounts. Consider implementing measures like limiting login attempts and enabling two-factor authentication to further enhance your site's security.
Choosing a secure web hosting provider is also crucial. Opt for a reputable company that takes proactive measures to protect their servers and offers advanced security configurations. Managed WordPress hosting can provide automatic backups, regular updates, and enhanced security features to ensure the safety of your website. Prioritize the security of your WordPress site by selecting a web hosting provider with a proven track record in WordPress security.
By following these WordPress security best practices and investing in secure WordPress hosting, you can protect your website from hackers, safeguard your data, and maintain the trust of your visitors. Don't compromise on the importance of WordPress security - prioritize the security of your WordPress blog today for a secure and successful online presence.
Important factors to ensure the best hosting are Speed, Support, Security. As your site grows you need to be sure your bigger, more popular website can still load fast and allow all large surges of higher traffic.
Hosting services are available in a wide range of prices ranging from a few dollars a month to thousands of dollars. A small business just getting a web presence, a shared hosting service is the best way to start. This gives you all you need regarding disc space, bandwidth and support. Leaving the support and management to the experts.
Virtual Private Server (VPS) is an open for a business that has outgrown shared services. Maybe you need more space or need to run applications that aren’t available on shared server. However you will need to manage it all yourself. After all a VPS is YOUR server so you are responsible for the running and management of the server and your websites. So a high level of knowledge is required.
Hosting prices can vary from just AU$4 / month up to AU$100 / month. This will depend on your needs and what you get for the plan.
What does Hosting and Support Mean?
All Hosting Providers offer similar offerings. Web and Email Hosting, Email Only, DNS Hosting. Basic customer service provides access to email, ticket and phone support.
The main difference is in support. Turnaround time on requests, Ticket Response times, Even just answering the phone. Some service providers will offer 24-hour phone support.
Bear in mind hosting support includes,
1. Server Maintenance and support
2. General troubleshooting and advice
3. Domain and hosting related management
4. Service renewals to ensure you don’t lose your domain or your services go offline.
5. Regular backups (used as a last resort for restores if required)
1. Website maintenance
2. Web development or changes to site
3. IT related issues such as fixing your email client, exporting email
However at Hosting Australia we do provide the above support but it will be charged at a reasonable rate. This means you don’t have to go find a developer to fix or maintain your website.
Managed Services.
Although the above support isn’t included in the normal hosting package, Hosting Australia can help with development and management with our Managed Services Packages. This allows you to leave it all to us. Your site is managed and updated on a regular basis to keep it all up to date and secure. It also includes changes to content and images as required but does not include design changes.
If you don’t want to use a monthly Managed Services Package then we will still support your site as required but quote on an ad hoc basis to work on the site when you need.
Estimate the amount of traffic you expect.
Some plans will include a limit on Bandwidth. This is the amount of traffic coming to your site. Just starting our your site won’t generate a lot of traffic but when it does upgrading your site to a higher level is very easy. Also your site may be seasonal. If your normal traffic is low but when you have an event and promote it you may find that your traffic suddenly spikes for a few weeks before the event and during. So you will need to allow for this and make sure you have enough bandwidth to handle the traffic. Rather than upgrading your hosting package you may just need to use an Add On package for the period of the event.
Where are the Servers?
Server location is important to a lot of people. Having servers overseas can affect your site speed and even more important support level due to time zones. Hosting Australia staff and servers are all in Australia and fully Australian owned.
There are some hosts that promote a simple web builder to instantly build a “great” site. Companies such as WIX, Weebly among others offer this server. What they don’t mention is that once the site is built it is locked to their servers because you are using their site building software. This doesn’t allow you to move your hosting if you find they don’t provide the support or service you expect. This means you need to build a whole new site just to move away from them.
You most probably will prefer the option to move if you need so a portable hosted CMS is the best way to go and your host can help you with migrating your site and email when you pick a new provider.
[et_pb_section fb_built="1" _builder_version="4.16" global_colors_info="{}"][et_pb_row _builder_version="4.16" background_size="initial" background_position="top_left" background_repeat="repeat" global_colors_info="{}"][et_pb_column type="4_4" _builder_version="4.16" custom_padding="|||" global_colors_info="{}" custom_padding__hover="|||"][et_pb_text _builder_version="4.17.4" background_size="initial" background_position="top_left" background_repeat="repeat" global_colors_info="{}"]
There is an easy answer to this question. Depends!
Most people will have 1 or 2 sites that they can easily manage with 1 or 2 cpanels. In fact some people can run 5 or more sites on the same Cpanel. This is done using Parked or Add On Domains.
This is fine if you own all the domains and want to keep costs down rather than running a Hosting Package for each domain. However if you have 5-10 or more domains and they belong to other people (friends, colleagues or customers) you would be better off choosing to be a reseller.
For a couple of reasons.
If you own all the domains it’s a good way to at least manage your sites through one portal but this also allows you to grow into a business and now provide the server to others.
Hosting Australia reseller packages start at $29/month which allows you 10 cpanel accounts. When you consider the average hosting package can be between $150 - $200 / year, you can very quickly start up a profitable business simply by bringing in some paying customers.
Web Hosting may not be your core business but if your business is web related such as graphics or web development why not offer the extra service to your customer and earn a little more to cover your costs of hosting your own sites?
Remember as a reseller this is your business. You can run it as you see fit… with in certain guidelines. Also you can charge whatever you want or not at all…. That’s all entirely up to you.
However since it is your business and they your customers, it is your responsibility to provide all support to your customers. It is your hosting company. You’re just using Hosting Australia’s infrastructure. Therefore you customers go to you for support not Hosting Australia.
That doesn’t mean we don’t provide support. You can come to us with anything you aren’t able to handle. However charges may apply. We still provide all the server support but any customer related or email / Web hosting problems will be charged for.
So there is that to consider because if you don’t have time or the knowledge or just don’t want to bother then being a reseller may not be for you. Or be a reseller and let us take care of your customers. We do provide support packages for resellers who just want to concentrate on their core business.
Being a reseller can be profitable but if you don’t want to take on all the responsibilities of supporting your customer hosting then perhaps an alternative is to become an affiliate.
This topic for another day
[/et_pb_text][/et_pb_column][/et_pb_row][/et_pb_section]
[et_pb_section fb_built="1" _builder_version="3.22" global_colors_info="{}"][et_pb_row _builder_version="3.25" background_size="initial" background_position="top_left" background_repeat="repeat" global_colors_info="{}"][et_pb_column type="4_4" _builder_version="3.25" custom_padding="|||" global_colors_info="{}" custom_padding__hover="|||"][et_pb_text _builder_version="4.14.7" background_size="initial" background_position="top_left" background_repeat="repeat" global_colors_info="{}"]
Did you know Hosting Australia Provides a free cPanel autoSSL? An SSL Certificate is a vital and powerful tool for securing your website and visually reassuring your visitors that their connection to your site is secure. Based on the SSL Certificate installed, most browsers and mobile devices will discourage and/or warn you of a website's security protocols in use. Furthermore, many search engines will give higher rankings to sites that have implemented an SSL Certificate (and use the https:// protocol rather than the non-secure https:// protocol).
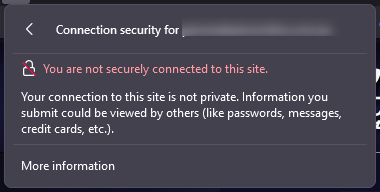
We'll explain the differences between "Free SSL" and "Dedicated SSL" Certificates in this article, which should help you decide which type of SSL Certificate is best for your website's security needs. Then, we'll assist you in installing cPanel's AutoSSL, a free SSL that is always enabled, so you can avoid browser warnings on your site.
Simply put, an SSL Certificate is a digital file that contains information used to authenticate the ownership of a website (or web server). It also includes a cryptographic key that has been supplied and authenticated by an authorised Certificate Authority (CA). This enables the visitor to quickly identify and trust a secure website.
This trust is represented by the more familiar "green padlock" displayed in the address bar. A green padlock (or, in some browsers, a solid, uncrossed padlock) indicates that the connection is properly encrypted for security.
In general, the two most widely accepted types of SSL are free SSLs and paid Dedicated SSL Certificates. In general, the encryption used by a Free SSL Certificate and a Dedicated SSL Certificate is the same.
What's the distinction? Without a dedicated IP address, free certificates use Server Name Indication (SNI). This means that multiple domains can use the same IP address while still using SSL. It should be noted that this type of certificate is not as widely accepted as an Advanced SSL with a dedicated IP address. This is since SNI is a relatively new extension that has only recently gained widespread support across browsers and devices. Some older browsers and devices may refuse to accept an SNI-enabled certificate.
Dedicated SSL Certificates frequently include more extensive validation. For example, an Extended Validation SSL Certificate would authenticate not only the domain owner but also the legitimacy of the business claiming to be the owner of the website. Although the encryption is the same, this additional layer of validation can help your visitors trust your website and business as a whole.
The level of acceptance provided by a free AutoSSL is adequate for most informational websites. Large-scale enterprises (such as an eCommerce store) that accept private data about their customers should consider purchasing a paid SSL certificate from a reputable certificate authority. In addition to being widely accepted in all browsers and devices, premium SSLs from certificate authorities frequently include support and warranties. This is why many payment processors insist on you purchasing specific, premium SSLs.
Hosting Australia offers a wide range of Premium rapidSSL’s that will be installed and managed by our support team. Check Out which SSL is best for your website HERE!
The below highlights some of the key differences between an AutoSSL and a purchased SSL, such as the popular RapidSSL
| Free AutoSSL Certificate | Purchased SSL Certificate |
| AutoSSL (cPanel, Comodo issued) certificate is valid for 90 days and renewed automatically in cPanel. More renewals, can mean more points of failure or issues. | Purchased SSL Certificates are valid for a minimum of 1 year. |
| AutoSSL Certificate doesn’t provide the site seal to display on your site and earn trust from your website users. | Purchased SSL Certificates provide a secured site seal for their SSL certificates, which earns the trust of your website visitors. |
| AutoSSL does not provide any kind of support - you will need to troubleshoot and manage as the end-user. | Most of the Purchased SSL Certificates provide customer support including sales, technical, and installation. |
| AutoSSL doesn't provide Organisation Validation (OV) and Extended Validation (EV). | Purchased SSL does provide Organisation Validation (OV) and Extended Validation (EV). |
| You can install an AutoSSL Certificate to secure your informative website or a blog. | If you are running your business, we recommend you to go with a Purchased Certificate as a more robust and trustworthy solution. |

Hosting Australia's Core and higher hosting packages include a free autoSSL certificate. This autoSSL can be found in the SSL/TLS Status section of your cPanel, under the Security heading.
If you see a red padlock, it means your autoSSL is not installed. Simply check the box and run AutoSSL; after a few moments, a pop-up will
appear informing you that your auto-ssl has been installed.
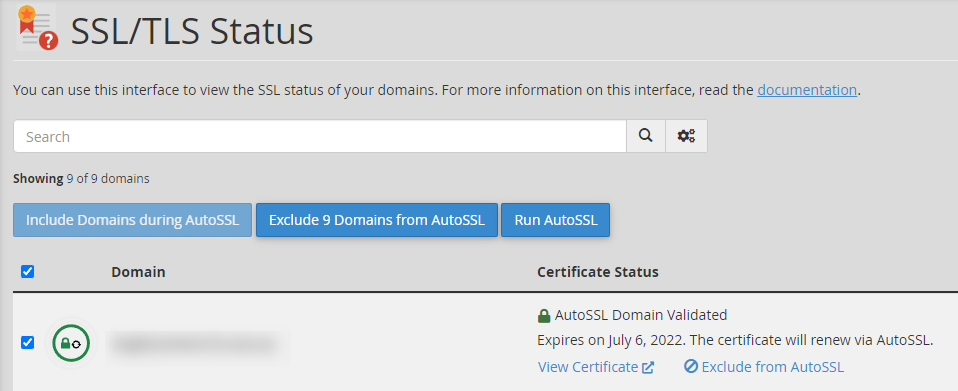
If you have any problems installing autoSSL, try troubleshooting using these methods.
To begin, ensure that your domain is pointed to our nameservers and eventually resolves to Hosting Australia's IP address. Check that your Content Delivery Network (CDN) is properly configured; some CDNs will require you to set up an SSL with them rather than with us. For more information on CDN-related errors, please see the section below. Here are some guides to help you ensure this is correctly configured.
Because your .htaccess file handles rewrite rules and redirects, it is frequently the source of Free SSL problems. .htaccess can be accessed through your File Manager; if you need help locating your File Manager, please see our guide HERE!
Because your plugins can modify the .htaccess file, they frequently cause conflicts. As a test, turn off any security plugins you're using.
When AutoSSL is enabled for an account and a domain or subdomain is added, the server initially generates a Self-Signed request and then works on obtaining an SSL certificate (based on Domain Name Validation).
[/et_pb_text][/et_pb_column][/et_pb_row][/et_pb_section]
Do you have a website and are getting the impression that it’s time to upgrade your hosting plan? Maybe you already know that you need to and you’re just waiting for the right moment to make the change. Maybe you’re not so sure about it. Whatever the reason for needing to upgrade your current hosting plan, you’re going to want to read on before making a final decision about whether or not you need to upgrade your current hosting plan. Hosting plays a critical role in the operation of your website. It’s the place where your site is stored and hosted. So, if you want your website to continue operating smoothly, you should make sure that you’re choosing the right hosting plan for your needs. Here are some of the signs that it’s time to upgrade your hosting plan.
Are you preparing to launch a new product? Are you allowing new members to join your membership site? Do you have a marketing campaign in the works that you're confident will be a success?
Make sure your website is prepared to handle more traffic than usual. The last thing you want prospective buyers, members, and social media followers to see is an error message—or a site that takes more than a few seconds to load.
If you're a new web designer or developer, you may have begun by adding your clients' domains to your shared hosting account. That might work for a while until it doesn't. If you manage numerous clients' domains from a single cPanel, you should consider upgrading your hosting package or transferring your clients to a reseller package.
Sites that load slowly are aggravating. If your site doesn't load in a few seconds, visitors are more likely to leave. In addition, if your site takes a long time to load, search engines will rank it lower in search results.
As a result, fewer individuals will be able to see what your website has to offer. If you've previously reviewed and optimised your basic web vitals, you might need to upgrade to a new hosting plan with faster server response times or a content delivery network to boost your site's speed.
Everybody appreciates enjoys a website with quality graphics, photos, and videos, and they all want them to load as soon as possible. It is best to optimise your images and videos for optimum functionality on your website. Compression and appropriate formatting can go a long way toward speeding up your site, but you may have more media than your current hosting package can manage at some point.
You might have come across the term “DNS TXT Record” as you browsed the web. If you haven’t heard about it before, you’ve probably come across a website that is using Text-Based DNS to work with their site. If you want to use this technique to work with your website, keep reading.
In this article, we will be discussing what a DNS TXT Record is, how it works, and examples of how you can use this record to work with your site. Keep reading to find out what a DNS TXT Record is, how it works and how you can use this record to work with your website.
A DNS TXT Record is a special type of DNS Record that is used to store extra data besides the standard DNS Record information. This record is stored in the DNS server and is accessible to the end-users of the DNS.
You can use the TLD (Top-level Domain) of the DNS server to define what type of data is stored in the TXT Record. Each TLD has a set of predefined TXT Records that you can use if you want to use a specific technique to work with your site.
For example, if you have a to validate your Domain name with Google and you are hosting with Hosting Australia, you can use Hosting Australia's DNS servers to create a DNS TXT record that points your Domain name to Google to validate your domain name.
TXT records can be used to ensure email security with the following records.
These records can be used to prevent phishing, spamming, and other malicious activity:
SPF is a standard email authentication method. SPF helps protect your domain against spoofing and helps prevent your outgoing messages from being marked as spam by receiving servers. SPF specifies the mail servers that are allowed to send emails for your domain. Receiving mail servers use SPF to verify that incoming messages that appear to come from your domain were sent by servers authorized by you.
| 2025.hosting-australia.com/ | TTL | Type | value: |
| 2025.hosting-australia.com/ | 3600 | TXT | v=spf1 ip4:192.243.61.237 ip6:2a05:d018:e3:8c00:bb71:dea8:8b83:851e |
DKIM Adds a digital signature to every outgoing message, which lets receiving servers verify the message actually came from your organization.
DKIM help's to protect your domain against spoofing and helps prevent your outgoing messages from being marked as spam. Spoofing is a type of email attack that forges the From address of an email message. A spoofed message appears to be from the impersonated organization or domain.
DKIM detects when a message has been modified, and when unauthorized changes are made to the message From: address.
Without DKIM, messages sent from your organization or domain are more likely to be marked as spam by receiving mail servers.
| 2025.hosting-australia.com/ | TTL | Type | value: |
| big-email._hosting-australia.com | 3600 | TXT | v=DKIM1; p=76E629F05F70 9EF665853333EEC3F5ADE69A 2362BECE4065 8267AB2FC3CB 6CBE |
DMARC: Let you tell receiving servers what to do with outgoing messages from your organization that doesn’t pass SPF or DKIM.
DMARC is a standard email authentication method. DMARC helps mail administrators prevent hackers and other attackers from spoofing their organization and domain. Spoofing is a type of attack in which the From address of an email message is forged. A spoofed message appears to be from the impersonated organization or domain.
DMARC also lets you request reports from email servers that get messages from your organization or domain. These reports have information to help you identify possible authentication issues and malicious activity for messages sent from your domain.
| 2025.hosting-australia.com/ | TTL | Type | value: |
| _dmarc.hosting-australia.com | 3600 | TXT | v=DMARC1;p=reject;pct=100;rua=mailto:postmaster@hosting-australia.com |
You can use TXT records to verify your domain with providers such as Microsoft, Google, Wix, Squarespace. This helps the provider find and validate the domain the provider gives you a record to add to your domain settings, when the provider sees that you’ve added the record, your domain ownership is confirmed and can allow other records to be added such as MX and CNAME.
| 2025.hosting-australia.com/ | TTL | Type | value: |
| businessmappingsolutions.com.au. | 3600 | TXT | google-gws-recovery-domain-verification=382251239 |
A CNAME record is a DNS record that allows you to associate one name with another name. When you create a CNAME record, you can point your domain to another record — or alias — that has the same name as itself.
The purpose of the CNAME record is to provide a way for you to leverage a domain name (to which you have the rights) for purposes that you do not own. For example, you may have the rights to build a site on http://hosting-australia.com, but you do not own the name itself. You can create a CNAME record pointing the domain name to your domain. The name used for the CNAME record (e.g. http://au.hosting-australia.com) is the alias (or target) for the domain name.
A common misunderstanding is that a CNAME record must always resolve to the same website as the domain it points to, although this isn't true. The CNAME record merely directs the client to the root domain's IP address. The web server will still handle the URL properly once the client reaches that IP address. For example, au.hosting-australia.com might have a CNAME that links to 2025.hosting-australia.com/, pointing the client to the IP address of 2025.hosting-australia.com/. When the client connects to that IP address, the webserver checks the URL and sees that it is au.hosting-australia.com, thus the blog page is delivered instead of the home page.
| au.hosting-australia.com | TTL | Type | value: |
| @ | 3600 | CNAME | is an alias of au.hosting-australia.com |
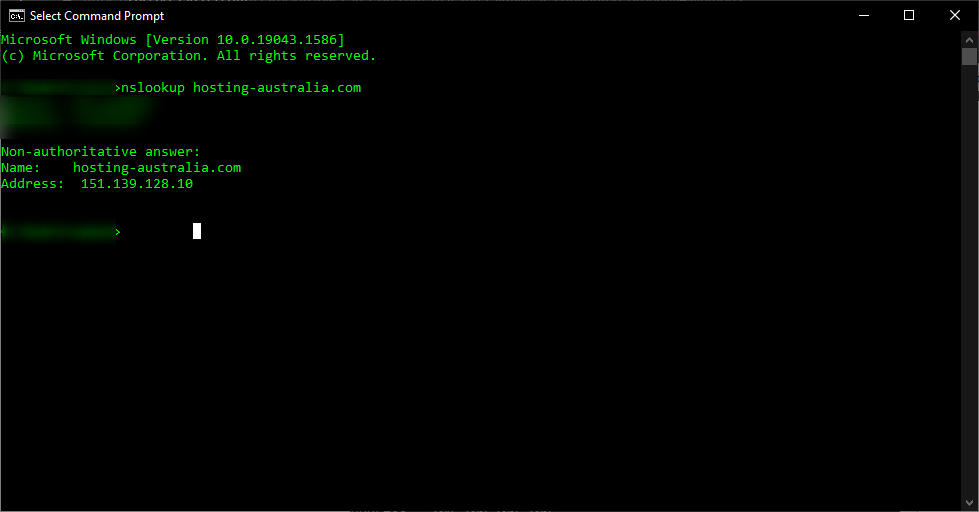
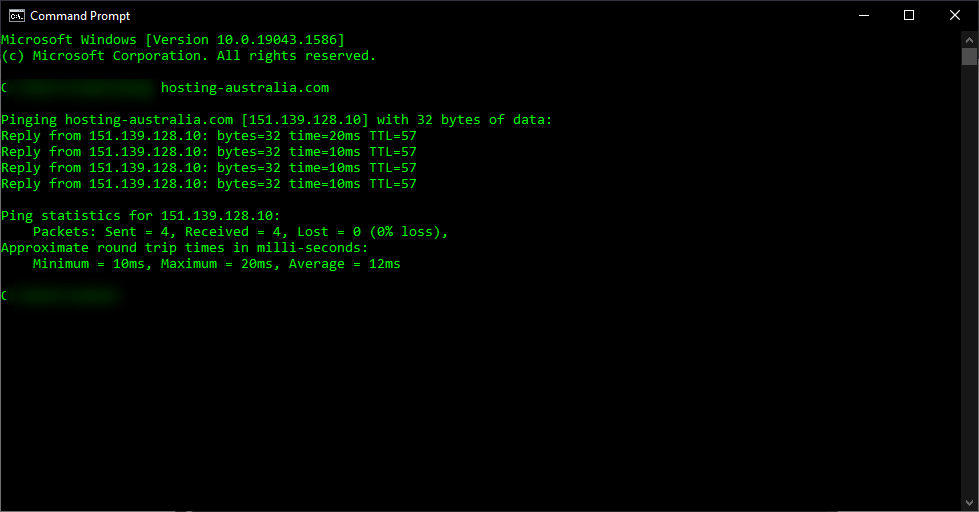
You can see that au.hosting-australia.com points to 2025.hosting-australia.com/ in this case, and assuming that it is based on our example, We know that the IP address 151.139.128.10 will eventually resolve to a record.
It's impractical to point a CNAME record to another CNAME record because it needs numerous DNS lookups before the domain can be loaded, slowing down the user experience, but it's feasible. For example, au.hosting-australia.com may have a CNAME record that linked to www.hosting-australia.com's CNAME record, which then pointed to the A record for 2025.hosting-australia.com/.
| au.hosting-australia.com | TTL | Type | value: |
| @ | 3600 | CNAME | is an alias of www.hosting-australia.com |
This option adds a step to the DNS lookup process that should be avoided if at all possible. Instead, both au. 2025.hosting-australia.com/ and www. 2025.hosting-australia.com/ 's CNAME records should link to 2025.hosting-australia.com/.
MX and NS records must point to an A record (for IPv4) or a AAAA record instead of a CNAME record (for IPv6). A mail exchange record (MX record) is a record that routes messages to a certain mail server. An NS record is a 'name server' record that specifies which DNS server for a domain is authoritative.
A domain name system (DNS) is a set of guidelines for mapping Internet Protocol (IP) addresses to domain names. A DNS A record is the resource record that maps an IPv4 address to a host name. The DNS server stores this information and can answer queries from other nodes on the Internet that are trying to resolve the IP address. This way, you don't have to memorize IP addresses for individual websites or servers on the internet. These A records are stored in a database called Zonefile.
There are different types of DNS records, and each one has a different function. It's important to know these records. But, this article will be focusing on the most common DNS record - The A record.
An A record is a mapping between a domain name and the IP address of the computer that hosts the domain. An A record is used to find the IP address of a computer connected to the internet using a domain name.
It’s quite simple, The A in A record stands for Address. The address you type every time you visit a website, send an email, connect to Twitter or Facebook, or do nearly anything else on the Internet is a collection of words connected by dots.
For example, to get our site Hosting Australia website, type www.hosting-australia.com into your browser. There is an A record on our name server that corresponds to the IP address 151.139.128.10. This implies that a request to www.hosting-australia.com from your browser gets forwarded to the server with the IP address 151.139.128.10.
A records are the most basic sort of DNS record, and they are one of the most commonly used records in DNS servers.
A records can be used for a variety of purposes, including providing redundancy and fallbacks by employing numerous A records for the same domain. Additionally, many names could point to the same IP address, in which case each would have its own A record.
The A record is essential to the functioning of the Internet since it maps a domain name to an IP address for devices connected to the Internet.
With the rise of email, we’ve all become accustomed to using a webpage to check our email. After all, you can't exactly turn your phone upside down and shake it to see if you've received an email.
This is where MX records come in. MX stands for mail exchange and an MX record is the address that tells other computers how to deliver emails sent to your domain name. Here's what you need to know about DNS MX records and how they work, so you can make sure your emails are being delivered correctly.
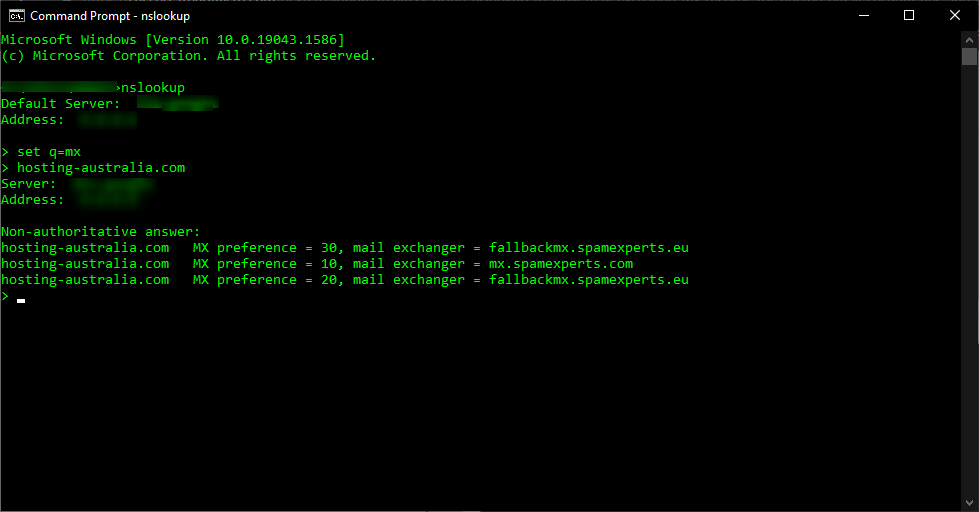
Email is directed to a mail server using a DNS'mail exchange' (MX) entry. As per the Simple Mail Transfer Protocol, the MX record specifies how email messages should be delivered (SMTP, the standard protocol for all emails). An MX record, like a CNAME record, must always point to a different domain such as mail. or the Google MX records listed below

For these MX records, the 'priority' numbers preceding the domains indicate preference; the lower the 'priority' value, the better. Because 10 is less than 20, the server will always attempt mailhost1 first. The server will fall back to mailhost2 in the event of a message send failure.
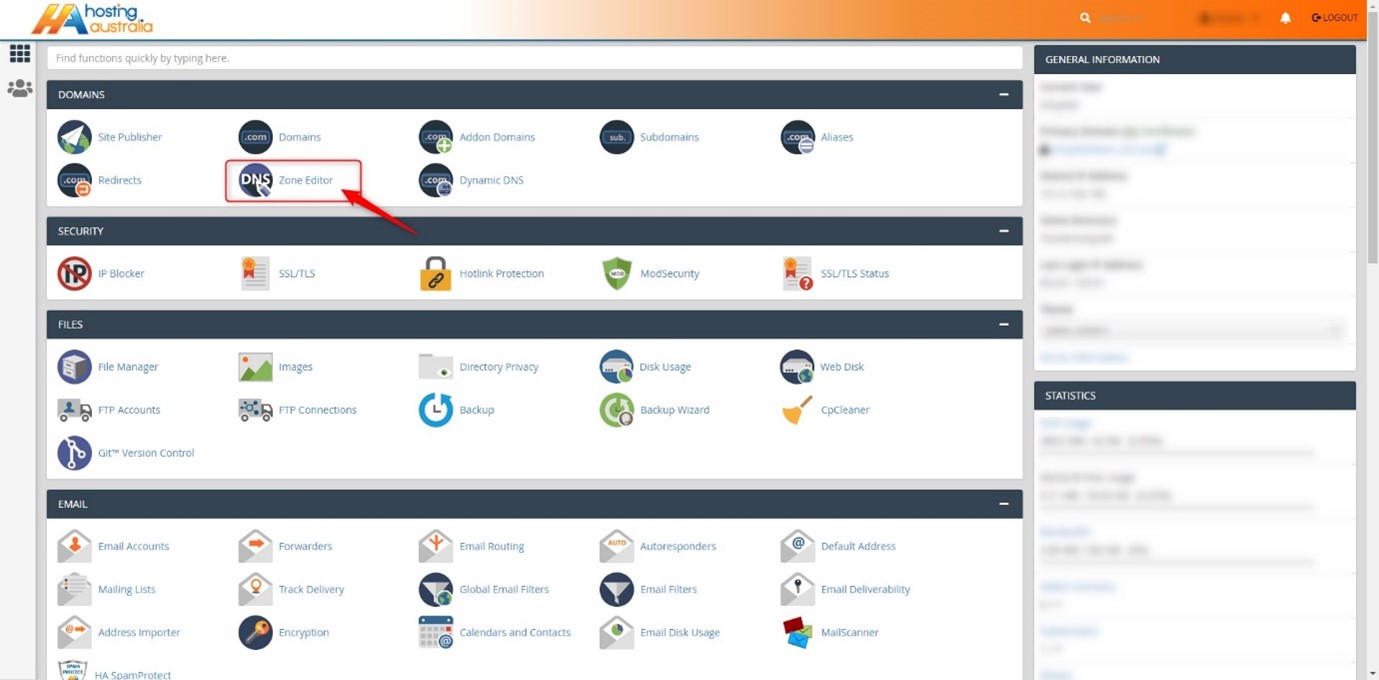
First, you will need to have access to your cPanel. If you are not sure how to access your cPanel, CLICK HERE.
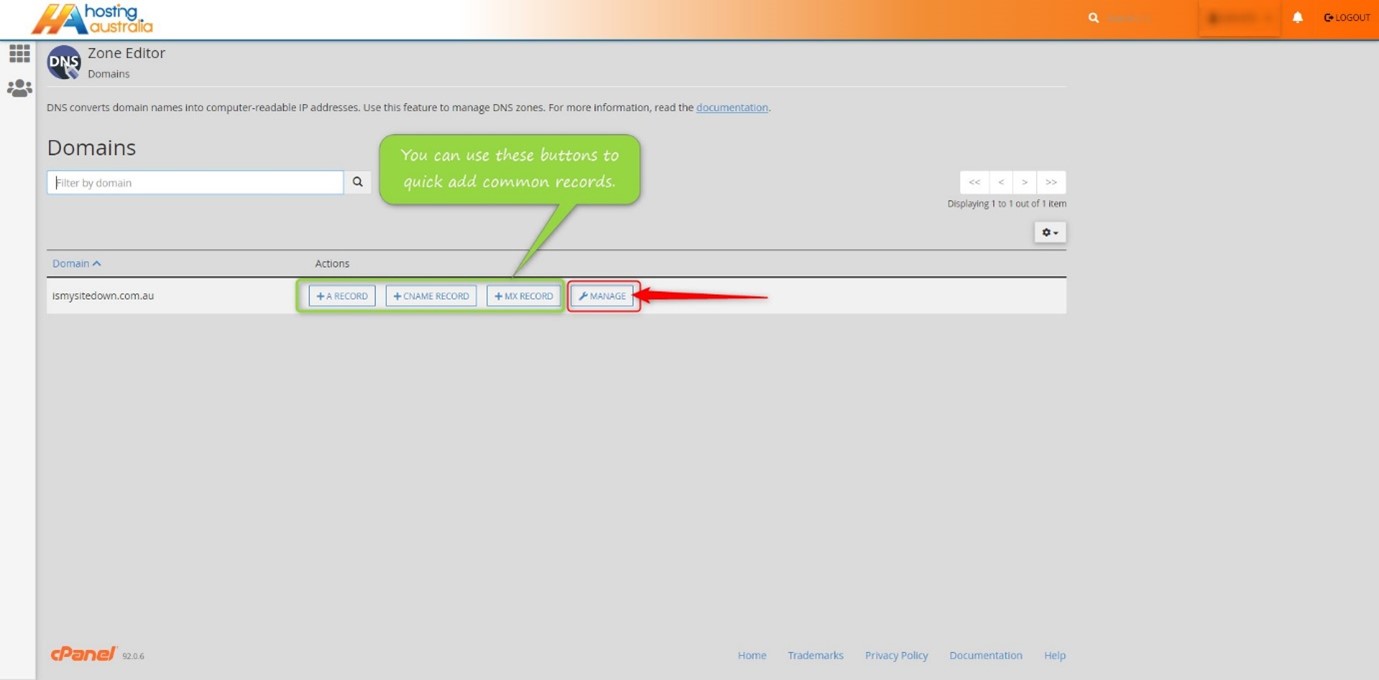
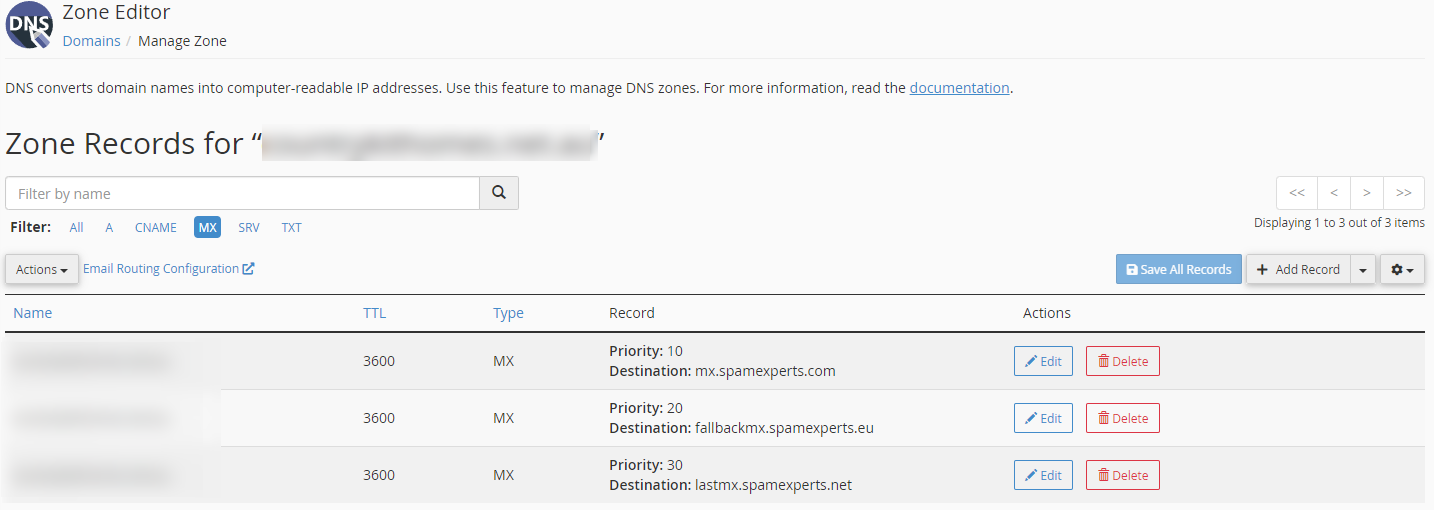
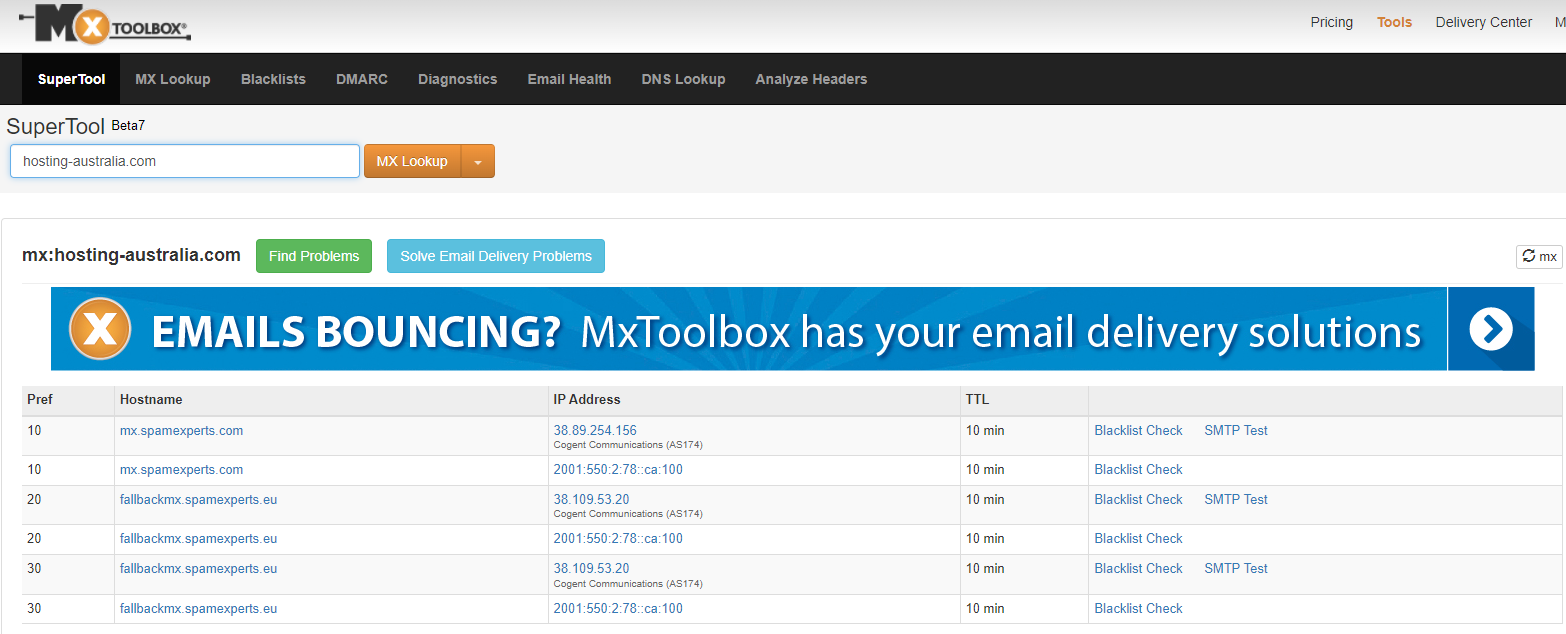
There are a lot of moving parts when it comes to managing your domain name. One of the most important things to have in order is an MX record. This is a record that controls how your email is delivered to your inbox. If you have a domain name, you have an MX record.
It's important that you know if your MX record is working correctly and if it's not, how to fix it. This is one of the simplest ways to keep your email flowing smoothly.
Have you ever wondered what an IP address is? An IP address is like your internet phone number. This number lets your computer talk to other computers over the internet. IP addresses usually look something like this: 192.168.1.1
If you want to visit a website, type in the web address (such as www.google.com) into your browser, and then hit enter to go there, your computer will contact another computer with the address of 192.168.1.1 and ask it for instructions on how to get there from where it is now.
a unique identifier is assigned to each machine in a network. Computers utilise unique identification to convey data to specific computers on a network, just like you would address a letter to send in the mail. The TCP/IP protocol is the standard for network communication in most networks today, including all computers on the internet. The IP address is a unique identifier for a computer in the TCP/IP protocol.
IP addresses are divided into two categories: IP Version 4 (IPv4) and IP Version 6 (IPv6) (IPv6). IPv4 addresses are used by all computers using IP addresses, and most also utilise the new IPv6 address scheme. The following are the distinctions between the two types of addresses:
IPv4 uses 32 binary bits to generate a single network address. Four integers separated by dots make up an IPv4 address. Each number is the decimal (base-10) representation of an octet, which is an eight-digit binary (base-2) number. Consider the following scenario: 14.203.8.145
To produce a single unique address on the network, IPv6 uses 128 binary bits. An IPv6 address is composed of eight groups of hexadecimal (base-16) numbers separated by colons, such as 2001:0db8:85a3:0000:0000:8a2e:0370:7334. To save space, groups of numbers with all zeros are frequently deleted, leaving a colon separator to highlight the gap (as in 2001:cdba::0370:7334).
The internet wasn't the commercial phenomenon it is now at the time of IPv4 addressing, and most networks were private and isolated from other networks around the world. With only 32 bits to establish a unique internet address when the internet first took off, there were fears that we'd run out of IP addresses before long. There are 232 potential IPv4 combinations, resulting in just over 4.3 billion distinct addresses. IPv6 increased the number of available addresses to a stress-relieving 2,128. Later, we'll look at how to decipher your computer's IPv4 or IPv6 addresses in more detail.
A dynamic or static IP address can exist. A static address is one that is assigned indefinitely. Internet service providers rarely assign static IP addresses. Static IPs can be assigned to devices on your local network, but doing so without a solid understanding of TCP/IP might lead to network problems. The most popular are dynamic addresses. The Dynamic Host Configuration Protocol (DHCP) is a network service that assigns them. Network gear, such as routers or dedicated DHCP servers, are commonly used to run DHCP.
A leasing system is used to issue dynamic IP addresses, which means the IP address is only operational for a certain time. The computer will automatically request a new lease if the current one expires. This may result in the computer receiving a new IP address as well, particularly if the computer was unplugged from the network between leases. Unless the computer alerts the user about a network IP address conflict, this process is normally invisible to the user (two computers with the same IP address). A conflict of address is uncommon, and today's technology usually resolves the issue automatically.
An IP address that does not change is known as a static IP address. When your device is given a static IP address, it usually stays that way until it is retired, or your network architecture changes. Servers and other key equipment typically utilise static IP addresses.
Internet Service Providers (ISPs) assign static IP addresses (ISPs). Depending on the terms of your service agreement, your ISP may or may not assign you a static IP address. Your options will be discussed later, but for now, except that a static IP address will increase the cost of your ISP contract.
A static IP address might be IPv4 or IPv6; the crucial quality is static in this situation. Every piece of networked equipment we have may one day have a unique static IPv6 address. We haven't arrived yet. For the time being, permanent addresses are normally assigned to static IPv4 addresses.
There are many reasons that you might need to have an IP address. For example, if you have an online business, you will need an IP address in order to connect to the internet. You can purchase one from your internet provider, or if you are looking to save some money, you can rent one. If you are running a business, it is important to know how IP addresses work, and how they can help you reach your goals.