Website speed and security are two critical factors that can make or break the online presence of small businesses. In today's digital landscape, where users expect fast-loading websites and protection from cyber threats, choosing the right web hosting provider is paramount. At Hosting Australia, we understand the importance of speed and security for small business websites, and we offer affordable and reliable web hosting services tailored to meet your unique needs.
Key Takeaways:
The Importance of Fast Web Hosting
When it comes to small business websites, fast web hosting is not just a luxury - it's a necessity. In today's digital world, users have become accustomed to instant gratification. They expect websites to load quickly and seamlessly, and if that expectation is not met, they will simply move on to the next option. Slow loading times can lead to high bounce rates, resulting in potential loss of customers and revenue.
Choosing a web hosting provider that prioritizes speed is crucial for small businesses. Look for providers that offer high-speed servers and optimized performance. These providers employ various techniques to ensure that your website loads quickly and efficiently. This includes utilizing caching technologies, minimizing server response time, and optimizing file sizes. By investing in fast web hosting, you can provide a smooth user experience for your website visitors and ultimately drive more conversions.
Additionally, fast web hosting can also have a positive impact on your search engine rankings. Search engines like Google take website speed into consideration when determining search results. A faster website can lead to higher rankings, increasing your online visibility and attracting more organic traffic. This can be especially beneficial for small businesses that are looking to compete with larger competitors in the online marketplace.
Benefits of Fast Web Hosting:
Enhancing Security with Multi-Factor Authentication
In the ever-evolving digital landscape, small businesses face increasing security threats. Protecting your website and sensitive data from cyber threats is crucial, and that's where multi-factor authentication (MFA) comes in. MFA adds an extra layer of security by requiring users to provide multiple forms of identification to gain access to your website.
MFA goes beyond traditional username and password combinations. It may involve additional factors such as biometric data, security tokens, or one-time passwords sent to a mobile device. By implementing MFA, small businesses can significantly reduce the risk of unauthorized access and safeguard their valuable information.
Web hosting providers play a vital role in enhancing security through MFA. They should offer robust and automated authentication systems, making it easy for small businesses to implement and manage multi-factor authentication. Additionally, phishing-resistant MFA and self-service options can further strengthen your website's security.
Benefits of Multi-Factor Authentication for Small Businesses
MFA offers several benefits for small businesses:
MFA is an essential security feature for small businesses. By partnering with a reliable web hosting provider that offers comprehensive multi-factor authentication options, small businesses can protect their websites, gain peace of mind, and build trust with their customers.
| MFA Features | Benefits |
| Automated authentication systems | Efficient and hassle-free implementation of MFA |
| Phishing-resistant MFA | Protects against phishing attacks, ensuring only authorized users access the website |
| Self-service options | Allows users to manage and update their authentication methods easily |
| Proactive monitoring | Constantly monitors for suspicious activity and provides real-time alerts |
Integration and Customization for Small Business Needs
Small businesses require web hosting solutions that offer seamless integration with their existing systems and the ability to customize their websites according to their unique needs. A reliable web hosting provider understands the importance of providing flexible integration options and customizable solutions to cater to the specific requirements of small businesses.
Native and Custom App Integrations
To enhance the functionality of their websites, small businesses need a web hosting provider that supports both native and custom app integrations. Native integrations allow businesses to seamlessly connect popular apps and tools to their websites, such as payment gateways, customer relationship management (CRM) software, and marketing automation tools. Custom app integrations provide the flexibility to connect proprietary or industry-specific applications to streamline business operations.
BYOD and Mobile Devices
In today's mobile-driven world, small businesses need a web hosting provider that offers support for Bring Your Own Device (BYOD) policies and ensures mobile responsiveness. This allows employees to access company resources and collaborate on the go, while ensuring a consistent and optimized user experience across all devices.
VPN or VPN-less Options
For small businesses that require secure remote access to their website's backend or sensitive data, a web hosting provider offering VPN (Virtual Private Network) or VPN-less options is crucial. VPNs provide a secure encrypted connection, allowing employees to access the website's backend securely from any location. VPN-less options, such as secure FTP (File Transfer Protocol) or SSH (Secure Shell) access, offer alternative secure methods for website management.
Single Sign-On (SSO) and Offline MFA for Windows Login
To simplify the login process and enhance security measures, small businesses can benefit from web hosting providers that support Single Sign-On (SSO) protocols. SSO allows users to authenticate once and gain access to multiple systems without the need for separate login credentials. Additionally, offline Multi-Factor Authentication (MFA) for Windows login adds an extra layer of security by requiring users to provide an additional authentication factor, such as a fingerprint or smartcard, to access their Windows accounts.
| Integration and Customization Features | Benefits |
| Native and Custom App Integrations | - Streamline business operations - Enhance website functionality - Integrate popular apps and tools |
| BYOD and Mobile Devices | - Enable employees to work on the go - Consistent user experience on all devices |
| VPN or VPN-less Options | - Secure remote access to backend and data - Flexibility in access methods |
| Single Sign-On (SSO) and Offline MFA for Windows Login | - Simplify login process - Enhance security measures |
By choosing a web hosting provider that offers integration and customization options, small businesses can optimize their online presence, streamline operations, and tailor their websites to meet their specific needs.
Meeting Compliance and Security Standards
Ensuring the security and compliance of small business websites is of utmost importance. Web hosting providers play a vital role in helping small businesses meet the necessary standards and protect their online assets. By offering robust security features and comprehensive reporting, reputable web hosting providers can assist small businesses in adhering to industry regulations and cyber liability insurance requirements.
One key aspect of meeting compliance and security standards is implementing strong multi-factor authentication (MFA) measures. Web hosting providers should offer automated authentication systems, phishing-resistant MFA, self-service options, and proactive monitoring to protect small business websites from cyber threats. These security features provide an additional layer of protection, ensuring that only authorized users can access sensitive data.
Benefits of Meeting Compliance and Security Standards:
In summary, small businesses operating in compliance-heavy industries or requiring cyber liability insurance must prioritize meeting security standards. By partnering with a reliable web hosting provider that offers robust security features and comprehensive reporting, small businesses can protect their websites and adhere to industry regulations.
| Benefits of Meeting Compliance and Security Standards |
| Protection from cyber threats |
| Industry recognition |
| Simplifying the audit process |
Domain Names and Web Hosting: Working Together
When it comes to establishing an online presence for small businesses, domain names and web hosting are two essential components that work hand in hand. A domain name serves as the digital address of a website, while web hosting provides the necessary infrastructure for storing all the files and code that make up the website. Understanding the relationship between domain names and web hosting is crucial for ensuring a seamless user experience.
Domain Names: The Digital Address
A domain name is like the street address of a website. It is the unique identifier that visitors use to access a website. For example, our domain name is "example.com". Choosing the right domain name is important for small businesses as it helps establish brand identity and improves search engine rankings. It is recommended to opt for a domain name that is short, easy to spell, and matches your business or brand name. Avoid using hyphens or creative spelling that can confuse visitors.
Web Hosting: The Digital House
Web hosting is the service that provides the necessary infrastructure and resources for a website to be accessible on the internet. It involves storing all the website files, databases, and code on a server that is connected to the internet. Web hosting providers offer different types of hosting plans to cater to the specific needs of small businesses. These plans vary in terms of storage space, bandwidth, scalability, and technical support. It is important to choose a reliable web hosting provider that can handle your website's traffic and provide security measures to protect your data.
The Connection: DNS Lookup
The connection between the domain name and web hosting is established through a process called DNS lookup. When a user enters a domain name in their web browser, the browser sends a request to the domain name server (DNS) to find the corresponding IP address of the web hosting server where the website is hosted. Once the IP address is obtained, the browser connects to the web hosting server and retrieves the website files, which are then displayed to the user.
In summary, domain names and web hosting go hand in hand to create a functional and accessible website for small businesses. Choosing the right domain name and web hosting provider is essential for establishing a professional online presence and providing a seamless user experience. By understanding the relationship between domain names and web hosting, small businesses can make informed decisions to ensure their website's success.
Choosing the Right Domain Name Registrar and Web Hosting Provider
When it comes to establishing an online presence for small businesses, choosing the right domain name registrar and web hosting provider is crucial. We understand the importance of fast and secure web hosting services that are affordable and reliable. That's why we recommend considering these key factors when making your decision.
Firstly, it's essential to select a reputable domain name registrar that offers fast DNS lookup and responsive customer support. A reliable registrar ensures that your domain name is easily accessible and resolves quickly, allowing visitors to reach your website without any delays.
Additionally, when choosing a domain name, opt for one that is short, simple to spell, and devoid of hyphens or creative spelling. This makes it easier for potential customers to remember and type into their browsers, reducing the risk of confusion and improving the overall user experience.
When it comes to web hosting, consider your website's functionality, expected traffic volume, email storage requirements, and testing capabilities. A reliable and secure web hosting provider will ensure the smooth operation and security of your small business website, providing you with the necessary resources to grow your online presence.
WordPress security is a critical concern for all website owners. With thousands of websites being blacklisted every day for malware and phishing, it's essential to implement the best practices for securing your WordPress blog. This guide will provide you with actionable steps and insights into WordPress security, including the importance of keeping WordPress updated, using strong passwords, and the role of web hosting in protecting your site.
Key Takeaways
Why WordPress Security is Important
The security of your WordPress site is of utmost importance in order to protect your website from hackers and prevent malware attacks. Security breaches can lead to data theft, the distribution of harmful malware, and even ransomware attacks. Not only can these breaches cause significant damage to your website and reputation, but they can also result in legal and financial consequences for your business.
In addition to protecting your own information, it is essential to consider your visitors' expectations. Internet users today are increasingly aware of the importance of online security, and they expect websites to provide a safe browsing experience. A secure website builds trust and credibility with your audience, increasing the likelihood of return visits and conversions. Furthermore, search engines like Google prioritize secure sites in their rankings, meaning that investing in WordPress security measures can also improve your website's visibility and organic traffic.
Protect Your Website from Hackers and Malware
By implementing proper WordPress security measures, you can safeguard your website and protect it from potential threats. This includes regularly updating WordPress, plugins, and themes, as updates often include security patches that address vulnerabilities. It also involves using strong passwords for your admin accounts, limiting login attempts, and enabling two-factor authentication to prevent unauthorized access.
Another key aspect of WordPress security is choosing a reliable web hosting provider. A secure hosting environment ensures that your website is hosted on servers that are protected against common threats and regularly updated with the latest security measures. Managed WordPress hosting, in particular, offers enhanced security features such as automatic backups, regular software updates, and advanced security configurations, providing an additional layer of protection for your site.
| Benefits of WordPress Security | Measures to Protect Your Website |
| 1. Protection against data theft and malware distribution | 1. Regularly update WordPress, plugins, and themes |
| 2. Enhanced trust and credibility with your audience | 2. Use strong passwords and limit login attempts |
| 3. Improved search engine visibility and organic traffic | 3. Enable two-factor authentication |
| 4. Legal and financial consequences | 4. Choose a reliable web hosting provider |
Keeping WordPress Updated
Regularly updating your WordPress installation, plugins, and themes is essential for maintaining a secure website. Updates often include security patches that address vulnerabilities and protect against potential threats. By keeping your WordPress site up to date, you minimize the risk of hacking attempts and ensure the stability of your site.
Updating WordPress is a straightforward process. Once a new version is released, you'll receive a notification in your WordPress dashboard. Simply click on the update button to initiate the update. It's important to back up your site before performing any updates to avoid any potential data loss. Additionally, it's crucial to update your plugins and themes as well. Outdated versions can expose your site to security risks.
To update your plugins, go to the "Plugins" section in your WordPress dashboard. If an update is available, you'll see a notification next to the plugin name. Click on the "Update Now" button to update the plugin. Similarly, for themes, navigate to the "Appearance" section and click on the "Themes" tab. If an update is available for your active theme, you'll see an update notification. Click on the "Update Now" button to update the theme.
| Key Actions | Purpose |
| Regularly update WordPress, plugins, and themes | Address vulnerabilities and protect against potential threats |
| Back up your site before performing updates | Minimize the risk of data loss |
| Update plugins in the "Plugins" section | Ensure plugins are up to date |
| Update themes in the "Appearance" section | Keep your active theme secure |
By prioritizing regular updates, you can strengthen the security of your WordPress site and stay protected against emerging threats.
Passwords and User Permissions
Creating strong passwords and managing user permissions are vital aspects of WordPress security. By implementing best practices in password management and user access control, you can significantly enhance the security of your WordPress site and protect it from unauthorized access.
Strong Passwords
Using strong, unique passwords is essential to prevent unauthorized access to your WordPress site. Avoid using commonly used passwords or personal information that can be easily guessed. Instead, create passwords with a combination of uppercase and lowercase letters, numbers, and special characters. Regularly updating passwords is also recommended to mitigate any potential risks.
Limit Login Attempts
Limiting the number of login attempts can deter hackers from using brute force attacks to gain access to your WordPress site. By setting a limit on the number of failed login attempts, you can effectively block repeated login attempts, making it more difficult for unauthorized users to guess or crack your password.
Two-Factor Authentication
Implementing two-factor authentication adds an extra layer of security to your WordPress login process. This authentication method requires users to provide an additional verification code, usually sent to their mobile device, after entering their password. By enabling two-factor authentication, you can ensure that only authorized individuals with both the password and the verification code can access your WordPress site.
Password Protect wp-admin and Login Pages
Another important security measure is to password protect the wp-admin directory and the login pages of your WordPress site. This additional layer of protection prevents unauthorized access to sensitive areas of your site, such as the WordPress admin panel. Password protecting these pages adds an extra barrier for potential hackers, making it more challenging for them to gain control of your WordPress site.
Table: User Permissions
| User Role | Capabilities |
| Administrator | Full access to all WordPress settings and functionality |
| Editor | Can create, edit, publish, and delete all posts and pages |
| Author | Can create, edit, publish, and delete their own posts |
| Contributor | Can write and edit their own drafts, but cannot publish them |
| Subscriber | Can only manage their profile and leave comments on your site |
Understanding user roles and permissions is crucial for controlling access to your WordPress site. By assigning appropriate user roles to individuals, you can limit their capabilities and ensure that only trusted users have access to critical administrative functions. Regularly review and update user permissions to maintain the security of your WordPress site.
The Role of Web Hosting
When it comes to securing your WordPress site, the choice of web hosting provider is crucial. A reliable and secure web hosting provider plays a significant role in protecting your website from potential threats. With web hosting security being a top priority, it's essential to choose a provider that offers advanced security features and robust infrastructure.
Managed WordPress hosting is an excellent option for ensuring the security of your WordPress site. By opting for managed hosting, you can benefit from automatic backups, regular updates, and enhanced security configurations. These features can significantly reduce the risk of security breaches and provide peace of mind.
The Benefits of Managed WordPress Hosting
Managed WordPress hosting offers several advantages when it comes to website security:
By choosing a secure web hosting provider, such as a reputable managed WordPress hosting service, you can enhance the security of your WordPress site and protect it from potential threats.
Conclusion
Securing your WordPress blog with hosting is of utmost importance to protect your website from hackers and malware. By implementing the best practices outlined in this guide, you can significantly enhance the security of your WordPress site and ensure a safe online presence.
Remember that WordPress security is an ongoing process, and it requires active vigilance. Keep your WordPress installation, plugins, and themes up to date to stay protected against potential threats. Additionally, use strong and unique passwords for your admin, FTP, and hosting accounts. Consider implementing measures like limiting login attempts and enabling two-factor authentication to further enhance your site's security.
Choosing a secure web hosting provider is also crucial. Opt for a reputable company that takes proactive measures to protect their servers and offers advanced security configurations. Managed WordPress hosting can provide automatic backups, regular updates, and enhanced security features to ensure the safety of your website. Prioritize the security of your WordPress site by selecting a web hosting provider with a proven track record in WordPress security.
By following these WordPress security best practices and investing in secure WordPress hosting, you can protect your website from hackers, safeguard your data, and maintain the trust of your visitors. Don't compromise on the importance of WordPress security - prioritize the security of your WordPress blog today for a secure and successful online presence.
Create an image featuring a shield or barrier with a WordPress logo inside, representing the idea of secure hosting.
Key Takeaways
Why WordPress Security is Important
The security of your WordPress site is of utmost importance in order to protect your website from hackers and prevent malware attacks. Security breaches can lead to data theft, the distribution of harmful malware, and even ransomware attacks. Not only can these breaches cause significant damage to your website and reputation, but they can also result in legal and financial consequences for your business.
In addition to protecting your own information, it is essential to consider your visitors' expectations. Internet users today are increasingly aware of the importance of online security, and they expect websites to provide a safe browsing experience. A secure website builds trust and credibility with your audience, increasing the likelihood of return visits and conversions. Furthermore, search engines like Google prioritize secure sites in their rankings, meaning that investing in WordPress security measures can also improve your website's visibility and organic traffic.
Protect Your Website from Hackers and Malware
By implementing proper WordPress security measures, you can safeguard your website and protect it from potential threats. This includes regularly updating WordPress, plugins, and themes, as updates often include security patches that address vulnerabilities. It also involves using strong passwords for your admin accounts, limiting login attempts, and enabling two-factor authentication to prevent unauthorized access.
Another key aspect of WordPress security is choosing a reliable web hosting provider. A secure hosting environment ensures that your website is hosted on servers that are protected against common threats and regularly updated with the latest security measures. Managed WordPress hosting, in particular, offers enhanced security features such as automatic backups, regular software updates, and advanced security configurations, providing an additional layer of protection for your site.
| Benefits of WordPress Security | Measures to Protect Your Website |
| 1. Protection against data theft and malware distribution | 1. Regularly update WordPress, plugins, and themes |
| 2. Enhanced trust and credibility with your audience | 2. Use strong passwords and limit login attempts |
| 3. Improved search engine visibility and organic traffic | 3. Enable two-factor authentication |
| 4. Legal and financial consequences | 4. Choose a reliable web hosting provider |
Keeping WordPress Updated
Regularly updating your WordPress installation, plugins, and themes is essential for maintaining a secure website. Updates often include security patches that address vulnerabilities and protect against potential threats. By keeping your WordPress site up to date, you minimize the risk of hacking attempts and ensure the stability of your site.
Updating WordPress is a straightforward process. Once a new version is released, you'll receive a notification in your WordPress dashboard. Simply click on the update button to initiate the update. It's important to back up your site before performing any updates to avoid any potential data loss. Additionally, it's crucial to update your plugins and themes as well. Outdated versions can expose your site to security risks.
To update your plugins, go to the "Plugins" section in your WordPress dashboard. If an update is available, you'll see a notification next to the plugin name. Click on the "Update Now" button to update the plugin. Similarly, for themes, navigate to the "Appearance" section and click on the "Themes" tab. If an update is available for your active theme, you'll see an update notification. Click on the "Update Now" button to update the theme.
| Key Actions | Purpose |
| Regularly update WordPress, plugins, and themes | Address vulnerabilities and protect against potential threats |
| Back up your site before performing updates | Minimize the risk of data loss |
| Update plugins in the "Plugins" section | Ensure plugins are up to date |
| Update themes in the "Appearance" section | Keep your active theme secure |
By prioritizing regular updates, you can strengthen the security of your WordPress site and stay protected against emerging threats.
Passwords and User Permissions
Creating strong passwords and managing user permissions are vital aspects of WordPress security. By implementing best practices in password management and user access control, you can significantly enhance the security of your WordPress site and protect it from unauthorized access.
Strong Passwords
Using strong, unique passwords is essential to prevent unauthorized access to your WordPress site. Avoid using commonly used passwords or personal information that can be easily guessed. Instead, create passwords with a combination of uppercase and lowercase letters, numbers, and special characters. Regularly updating passwords is also recommended to mitigate any potential risks.
Limit Login Attempts
Limiting the number of login attempts can deter hackers from using brute force attacks to gain access to your WordPress site. By setting a limit on the number of failed login attempts, you can effectively block repeated login attempts, making it more difficult for unauthorized users to guess or crack your password.
Two-Factor Authentication
Implementing two-factor authentication adds an extra layer of security to your WordPress login process. This authentication method requires users to provide an additional verification code, usually sent to their mobile device, after entering their password. By enabling two-factor authentication, you can ensure that only authorized individuals with both the password and the verification code can access your WordPress site.
Password Protect wp-admin and Login Pages
Another important security measure is to password protect the wp-admin directory and the login pages of your WordPress site. This additional layer of protection prevents unauthorized access to sensitive areas of your site, such as the WordPress admin panel. Password protecting these pages adds an extra barrier for potential hackers, making it more challenging for them to gain control of your WordPress site.
Table: User Permissions
| User Role | Capabilities |
| Administrator | Full access to all WordPress settings and functionality |
| Editor | Can create, edit, publish, and delete all posts and pages |
| Author | Can create, edit, publish, and delete their own posts |
| Contributor | Can write and edit their own drafts, but cannot publish them |
| Subscriber | Can only manage their profile and leave comments on your site |
Understanding user roles and permissions is crucial for controlling access to your WordPress site. By assigning appropriate user roles to individuals, you can limit their capabilities and ensure that only trusted users have access to critical administrative functions. Regularly review and update user permissions to maintain the security of your WordPress site.
The Role of Web Hosting
When it comes to securing your WordPress site, the choice of web hosting provider is crucial. A reliable and secure web hosting provider plays a significant role in protecting your website from potential threats. With web hosting security being a top priority, it's essential to choose a provider that offers advanced security features and robust infrastructure.
Managed WordPress hosting is an excellent option for ensuring the security of your WordPress site. By opting for managed hosting, you can benefit from automatic backups, regular updates, and enhanced security configurations. These features can significantly reduce the risk of security breaches and provide peace of mind.
The Benefits of Managed WordPress Hosting
Managed WordPress hosting offers several advantages when it comes to website security:
By choosing a secure web hosting provider, such as a reputable managed WordPress hosting service, you can enhance the security of your WordPress site and protect it from potential threats.
Conclusion
Securing your WordPress blog with hosting is of utmost importance to protect your website from hackers and malware. By implementing the best practices outlined in this guide, you can significantly enhance the security of your WordPress site and ensure a safe online presence.
Remember that WordPress security is an ongoing process, and it requires active vigilance. Keep your WordPress installation, plugins, and themes up to date to stay protected against potential threats. Additionally, use strong and unique passwords for your admin, FTP, and hosting accounts. Consider implementing measures like limiting login attempts and enabling two-factor authentication to further enhance your site's security.
Choosing a secure web hosting provider is also crucial. Opt for a reputable company that takes proactive measures to protect their servers and offers advanced security configurations. Managed WordPress hosting can provide automatic backups, regular updates, and enhanced security features to ensure the safety of your website. Prioritize the security of your WordPress site by selecting a web hosting provider with a proven track record in WordPress security.
By following these WordPress security best practices and investing in secure WordPress hosting, you can protect your website from hackers, safeguard your data, and maintain the trust of your visitors. Don't compromise on the importance of WordPress security - prioritize the security of your WordPress blog today for a secure and successful online presence.
One of the primary functions of SiteLock is to scan your website for malware and promptly remove any malicious code or scripts. Cyber criminals are constantly evolving their tactics, and even the most secure websites can fall victim to malware attacks. SiteLock acts as a virtual shield, actively monitoring your site and eliminating any security threats before they can wreak havoc.
SiteLock not only identifies and eliminates malware but also optimizes your website's performance. It ensures that your website runs smoothly and efficiently, providing visitors with a seamless browsing experience. By cleaning up unnecessary files and databases, SiteLock helps your website load faster, reducing bounce rates and increasing customer satisfaction.
Distributed Denial of Service (DDoS) attacks can overwhelm your website with traffic, causing it to crash and disrupting your online services. SiteLock offers robust DDoS protection, detecting and mitigating these attacks in real-time. By safeguarding your website against DDoS attacks, SiteLock ensures that your site remains accessible to legitimate users, even during malicious traffic surges.
For websites that handle sensitive customer information, such as personal details and payment data, security is paramount. SiteLock encrypts data transmission, making it extremely challenging for hackers to intercept and misuse customer information. This encryption ensures that your customers can trust your website with their data, fostering customer loyalty and confidence in your brand.
SiteLock plays a vital role in improving your website's search engine optimization (SEO) rankings. Search engines prioritize secure websites, considering them trustworthy and reliable sources of information. By securing your website with SiteLock, you not only protect your visitors but also enhance your visibility in search engine results, potentially attracting more organic traffic.
SiteLock doesn't just offer one-time protection; it provides continuous security monitoring for your website. Regular scans and reports keep you informed about your website's security status, allowing you to take immediate action if any vulnerabilities are detected. This proactive approach ensures that your website remains secure, giving you peace of mind and allowing you to focus on your core business activities.
In conclusion, SiteLock is not just an additional security measure; it is a fundamental necessity for any website owner. By safeguarding your website from malware, optimizing its performance, protecting against DDoS attacks, securing customer data, boosting SEO rankings, and offering continuous monitoring, SiteLock empowers your website to thrive in the digital landscape. Investing in SiteLock is an investment in the credibility, trustworthiness, and longevity of your online presence. Don't wait until it's too late – fortify your website with SiteLock today and ensure a secure and seamless experience for both you and your visitors.
Thanks to Hosting Australia’s SPAM Protect, your emails will be safer than ever before. We keep developing our technology so that it can block more of those pesky messages from finding their way into inboxes and on computer screens everywhere!
SPAMProtect helps protect inboxes, users, and IPs from the full range of email hazards while saving resources and costs. With competitive, per-domain pricing, you can have piece of mind, with minimal costs.
SPAMProtect offers a variety of services to keep your inbox flowing smoothly, even when you’re not online or our service goes down! You can store messages so they don’t disappear without being read and then retry delivery during outages for an uninterrupted flow of mail!
SPAMProtect Incoming Filtering software offers full inbox protection against spam, viruses and malware with the help of advanced algorithms, smart learning and spam pattern detection methods.
Hosting Australia Spam Protect provides enterprise grade protection against inbound spam, viruses, phishing, malware, ransomware and other email-based threats. Clean and safe inboxes with additional email continuity. Click Here to order and setup Spam Protect on your account.
Cyber threats are a constant concern, protecting your online presence has never been more critical. One of the most powerful tools at your disposal is a Virtual Private Network (VPN). In this article, we will explore the reasons why using a VPN is essential in today's internet landscape.
**1. ** Privacy Protection:
Privacy is a fundamental right, and it shouldn’t be compromised online. However, the internet is rife with prying eyes, including government agencies, hackers, and even your Internet Service Provider (ISP). A VPN encrypts your internet connection, making it nearly impossible for anyone to intercept your data. This means your online activities, personal information, and sensitive data remain secure and private.
**2. ** Secure Data Transmission:
When you connect to a public Wi-Fi network, such as those in cafes, airports, or hotels, your data is incredibly vulnerable. Hackers often exploit these networks to intercept user data. By using a VPN, you create a secure tunnel for your data to travel through. This encryption ensures that even if someone manages to intercept the data, it would be unreadable and useless to them.
**3. ** Bypass Geo-restrictions:
Have you ever encountered the frustrating message, “This content is not available in your region”? Streaming services, websites, and social media platforms often restrict content based on your geographical location. VPNs allow you to mask your IP address, making it appear as if you’re browsing from a different location. This grants you access to geo-restricted content, expanding your internet experience significantly. NB: some VPN services can still be detected by geo-restricted sites. Usually free VPNs because they won't allow you to connect via a preferred location but some random one. So for this you may need to use a paid license.
Hosting Australia provides a VPN service thru NordVPN.
**4. ** Online Anonymity:
In the age of targeted ads and data mining, maintaining anonymity online is a challenge. A VPN hides your real IP address, replacing it with the IP address of the VPN server you’re connected to. This not only protects your identity but also prevents websites and online services from tracking your online behavior and personal preferences.
**5. ** Enhanced Security:
VPNs not only protect your data from hackers but also shield you from other online threats like phishing attacks and malicious websites. Some advanced VPN services come with built-in malware and ad blockers, providing an additional layer of security against online threats.
**6. ** Safe Torrenting:
If you are a fan of torrents, a VPN is your best friend. Torrenting without a VPN exposes your IP address to other users, making you susceptible to legal issues and copyright infringement notices. A VPN masks your IP, allowing you to torrent safely and anonymously.
**7. ** Business Use:
For businesses, especially those with remote teams, VPNs are indispensable. They enable employees to securely access company resources and confidential data from anywhere in the world. By encrypting connections, VPNs ensure that sensitive business information remains protected from unauthorized access.
In conclusion, a VPN is no longer just a tool for the tech-savvy; it’s a necessity for anyone who values their online privacy and security. With cyber threats on the rise and privacy becoming increasingly scarce, investing in a reputable VPN service is a proactive step toward safeguarding your digital life. By encrypting your connection, bypassing geo-restrictions, ensuring online anonymity, and providing enhanced security, a VPN empowers you to enjoy the internet without fear, knowing that your online presence is private and protected.
When launching a new website, there are several steps that you must take to keep it safe. By following some basic security measures, you can save yourself a lot of headaches and trouble. In addition, making sure that your website is secure before you add any content is also important. In this article, we'll cover five of the most important security practices for your new website.
Use a Secure Content Management System CMS
A secure CMS helps keep your website safe from cyber-attacks. Its security features include strict controls over access and the ability to isolate users. To ensure your website's security, only a select group of users can edit, add, or delete content. Administrators should also follow procedures for offboarding unauthorized users. A secure CMS also separates its backend from the front end, which limits the damage in the event of a breach.
When choosing a CMS, you'll want to consider the size of your organization, the number of users, and the level of security you'd like to provide. Another consideration is the variety of digital content your business plans to share. All of this data should be easily indexed by search engines. You'll also want to get input from employees, leadership, the marketing department, and IT staff before you select a CMS.
The main reason CMSes are vulnerable is because most of the software they use is open source. This makes them a prime target for hackers. Additionally, many of these platforms have been vulnerable for a long time because they're not updated frequently. While they have some advantages, they also come with a number of flaws, which makes them a vulnerable target. In addition to this, open source CMSes have a lower degree of accountability than their commercial counterparts.
Control Who Has Access
When you first get a new website, the most important thing is to control who has access to it. You should not give your site administrator access to every feature. The CMS should also allow you to change the permissions of contributors and editors. CMSes generally let you control this. However, you need to be careful about what access each group should have. If you're creating a website for a non-profit, for example, you should set permissions for your readers.
Choose a Secure Reliable Hosting Platform
If you want to start a website for your business, you'll need to choose a secure, reliable hosting platform. Fortunately, there are plenty of options available. Bluehost, for example, offers shared and VPS hosting plans. This company offers blazing-fast SSDs, security monitoring, and 24/7 network security. It also offers a simple management console and one-click deployment tools.
To begin securing your website, you'll need an SSL certificate. An SSL certificate will create an encrypted link between your web server and your customers' browser. This secure link helps protect sensitive data from bad actors. When a customer visits your website, a green padlock will appear in the address bar. Some web hosts provide this security for free, while others charge up to $100 a year.
Before choosing a web hosting plan, compare prices and features. Also, make sure there are no hidden charges or blockages. If you are unsure, consider going with a free trial. This way, you can see whether the plan you select is suitable for your needs. If you like it, you can then choose to purchase the plan. If it's a good fit, you can also upgrade to a premium hosting plan.
As with all things, performance and security are important when it comes to the web hosting platform you choose for your new website. Choose a web hosting provider that understands the risks and has a commitment to keeping your site secure and protected. Your new website should also be protected by an SSL certificate, which means it will be backed up to a distant server in the event of a breach or other attack. You should also choose a web hosting provider that will offer ongoing technical support.
Install High-Grade Security Features
Effective website security requires design efforts across the entire website, including client-side code and server configuration. Besides using SSL, you can also install server-side web frameworks that can enable robust defense mechanisms. Another way to keep your website secure is to implement HTTPS (Hyper Text Transfer Protocol Secure). Using publicly available vulnerability scanner tools can help you identify obvious mistakes that can compromise your website. These vulnerabilities can lead to data theft, identity theft, and even malware infection.
In addition to securing your site against hackers, you should also use secure passwords for all users. Your passwords should be lengthy and contain special characters and numbers, and should not contain any obvious keywords. You should hold yourself and your team accountable for using secure passwords, and encourage everyone to use them. You should also consider offering a bug bounty to encourage people to report security issues. You should also make sure your website uses SSL to protect sensitive data.
Keep Everything Updated
The first step to securing your new website is to keep all of your software and hardware up to date. Companies and software developers constantly release patches and updates to plug security holes. If you don't update your software, you leave yourself vulnerable. Fortunately, most hosts will make it easy for you to update the software on your site. They will also remind you when a new version is available. Keeping everything up to date will help you prevent any website hacking attempts and keep your visitors safe.
Keeping everything up to date is particularly important for databases and applications. These are likely points of entry for hackers, so it is imperative to keep them updated. Additionally, it's important to keep your file structure organized, so you can easily identify changes and remove old files. Keeping everything updated will also save you money in the long run. Here are some other tips for keeping your website up to date:
Ensure that you backup your website on a regular basis. You'll want to ensure that you have off-site backups. Having these backups is essential, especially if there's a problem with your web host's data center. Consider your website as your virtual office - it's a vital part of your business, so you must protect it accordingly. You should also ensure that you regularly update your integrations and third-party applications.
Final Thoughts
After you set up your new website, you should take some basic steps to protect it. These protective measures are the easiest to implement and set up your website reasonably well. Hackers don't manually hack websites, they create bots to sniff out vulnerable sites and do the hacking for them. The bots aren't sentient, but they're programmed to do certain actions. By following these tips, you can secure your new website from hackers.
[et_pb_section fb_built="1" _builder_version="4.16" custom_padding="||111px|||" global_colors_info="{}"][et_pb_row _builder_version="4.16" background_size="initial" background_position="top_left" background_repeat="repeat" custom_margin="|auto|11px|auto||" custom_padding="||68px|||" global_colors_info="{}"][et_pb_column type="4_4" _builder_version="4.16" custom_padding="|||" global_colors_info="{}" custom_padding__hover="|||"][et_pb_text _builder_version="4.16" background_size="initial" background_position="top_left" background_repeat="repeat" global_colors_info="{}"]Having your website hacked or infected by malware is probably one of the worst things that can happen to any website, and its every site owner worst nightmare. Website get infected by malware or malicious software all the time, the best way is to prevent it with a best WordPress malware removal plugin. If you see there is a problem with your site you install and activate a plugin to clean your sit. However if you wait until your site is infected it can be too late to save your it. Its always best to install a malware plugin when you build the site or any time you like, preferably before you get infected. Its why they say prevention is better than cure. Sometimes the cure can mean a complete rebuild of your site because its too far gone to guarantee you have cleaned it completely.
Therefore we have list a couple options that we use and fin them to be effective in keep the hackers at bay. The one negative you will see is that you will suddenly get a lot of email telling you every time someone is trying to log into your site. This may be annoying but trust us this is a good thing. Because it means the plugin is working. It just highlights that people are trying to hack your site and our servers all the time. You just don't see it but now you do. This does get annoying so you can normally fix it by setting the plugin to only notify you when someone unauthorised DOES login. That's when you need to know. The strength of these plugins is that if you install them early they prevent people accessing your site and files.
Keeping your WordPress site and plugins up to date with regular updates plus a security plugin gives you the best chance to protect your site.
We have included some products that we use and recommend for your site security.
[/et_pb_text][et_pb_text _builder_version="4.17.4" _module_preset="default" header_font="|||||on|||" header_font_size="50px" custom_margin="50px||30px||false|false" global_colors_info="{}"]
[/et_pb_text][et_pb_image src="http://hosting-australia.com/wp-content/uploads/2022/07/wordfence-malware-scan-removal.webp" title_text="wordfence-malware-scan-removal" _builder_version="4.17.4" _module_preset="default" global_colors_info="{}"][/et_pb_image][et_pb_text _builder_version="4.17.4" _module_preset="default" hover_enabled="0" global_colors_info="{}" sticky_enabled="0"]
Wordfence includes a firewall and malware scanner that were built to protect WordPress. Wordfences major function is to prevent unauthorised logins. This prevent most attacks because they simply can't get it. However Wordfence also provides malware scanning to find any suspicious content in our web files
It is a free plugin but the a paid version is available to provide malware fixes and to block countries that you don't want access from.
An additional feature now available is 2FA to provide an extra layer of security when trying to log in. Wordfence is the most comprehensive WordPress security solution available. Malware scanner checks core files, themes and plugins for malware, bad URLs, backdoors, SEO spam, malicious redirects and code injections.
[/et_pb_text][et_pb_text _builder_version="4.17.4" _module_preset="default" header_font="|||||on|||" header_font_size="50px" custom_margin="100px||30px||false|false" global_colors_info="{}"]
[/et_pb_text][et_pb_image src="http://hosting-australia.com/wp-content/uploads/2022/07/logo-rsfirewall-for-wordpress.png" title_text="logo-rsfirewall-for-wordpress" _builder_version="4.17.4" _module_preset="default" custom_margin="||||false|false" custom_padding="||||false|false" global_colors_info="{}"][/et_pb_image][et_pb_text _builder_version="4.17.4" _module_preset="default" hover_enabled="0" global_colors_info="{}" sticky_enabled="0"]
RSFirewall was originally built for Joomla sites and most of their products are geared to Joomla and worked very well in protecting sites and blocking countries. However they now provide a firewall version for WordPress and it appears to work just as well as it did for Joomla.
RSFirewall is a paid plugin but if you order it from Hosting Australia we can add it to your wordpress site for a discounted price.
2FA login and Country blocking comes standard with RSFirewall so only one low price to pay to have your site secured.
[/et_pb_text][/et_pb_column][/et_pb_row][/et_pb_section]
[et_pb_section fb_built="1" _builder_version="3.22" global_colors_info="{}"][et_pb_row _builder_version="3.25" background_size="initial" background_position="top_left" background_repeat="repeat" global_colors_info="{}"][et_pb_column type="4_4" _builder_version="3.25" custom_padding="|||" global_colors_info="{}" custom_padding__hover="|||"][et_pb_text _builder_version="4.14.7" background_size="initial" background_position="top_left" background_repeat="repeat" global_colors_info="{}"]
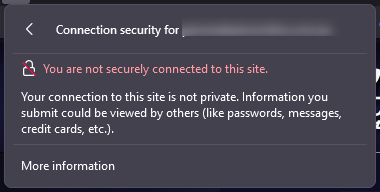
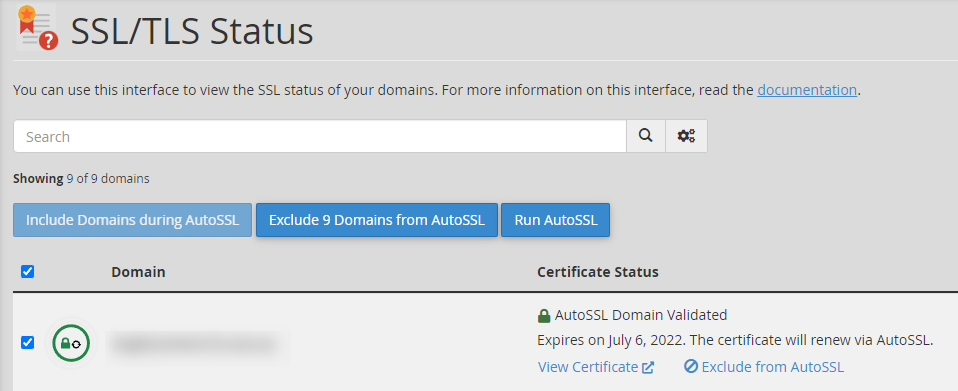
Did you know Hosting Australia Provides a free cPanel autoSSL? An SSL Certificate is a vital and powerful tool for securing your website and visually reassuring your visitors that their connection to your site is secure. Based on the SSL Certificate installed, most browsers and mobile devices will discourage and/or warn you of a website's security protocols in use. Furthermore, many search engines will give higher rankings to sites that have implemented an SSL Certificate (and use the https:// protocol rather than the non-secure https:// protocol).
We'll explain the differences between "Free SSL" and "Dedicated SSL" Certificates in this article, which should help you decide which type of SSL Certificate is best for your website's security needs. Then, we'll assist you in installing cPanel's AutoSSL, a free SSL that is always enabled, so you can avoid browser warnings on your site.
Simply put, an SSL Certificate is a digital file that contains information used to authenticate the ownership of a website (or web server). It also includes a cryptographic key that has been supplied and authenticated by an authorised Certificate Authority (CA). This enables the visitor to quickly identify and trust a secure website.
This trust is represented by the more familiar "green padlock" displayed in the address bar. A green padlock (or, in some browsers, a solid, uncrossed padlock) indicates that the connection is properly encrypted for security.
In general, the two most widely accepted types of SSL are free SSLs and paid Dedicated SSL Certificates. In general, the encryption used by a Free SSL Certificate and a Dedicated SSL Certificate is the same.
What's the distinction? Without a dedicated IP address, free certificates use Server Name Indication (SNI). This means that multiple domains can use the same IP address while still using SSL. It should be noted that this type of certificate is not as widely accepted as an Advanced SSL with a dedicated IP address. This is since SNI is a relatively new extension that has only recently gained widespread support across browsers and devices. Some older browsers and devices may refuse to accept an SNI-enabled certificate.
Dedicated SSL Certificates frequently include more extensive validation. For example, an Extended Validation SSL Certificate would authenticate not only the domain owner but also the legitimacy of the business claiming to be the owner of the website. Although the encryption is the same, this additional layer of validation can help your visitors trust your website and business as a whole.
The level of acceptance provided by a free AutoSSL is adequate for most informational websites. Large-scale enterprises (such as an eCommerce store) that accept private data about their customers should consider purchasing a paid SSL certificate from a reputable certificate authority. In addition to being widely accepted in all browsers and devices, premium SSLs from certificate authorities frequently include support and warranties. This is why many payment processors insist on you purchasing specific, premium SSLs.
Hosting Australia offers a wide range of Premium rapidSSL’s that will be installed and managed by our support team. Check Out which SSL is best for your website HERE!
The below highlights some of the key differences between an AutoSSL and a purchased SSL, such as the popular RapidSSL
| Free AutoSSL Certificate | Purchased SSL Certificate |
| AutoSSL (cPanel, Comodo issued) certificate is valid for 90 days and renewed automatically in cPanel. More renewals, can mean more points of failure or issues. | Purchased SSL Certificates are valid for a minimum of 1 year. |
| AutoSSL Certificate doesn’t provide the site seal to display on your site and earn trust from your website users. | Purchased SSL Certificates provide a secured site seal for their SSL certificates, which earns the trust of your website visitors. |
| AutoSSL does not provide any kind of support - you will need to troubleshoot and manage as the end-user. | Most of the Purchased SSL Certificates provide customer support including sales, technical, and installation. |
| AutoSSL doesn't provide Organisation Validation (OV) and Extended Validation (EV). | Purchased SSL does provide Organisation Validation (OV) and Extended Validation (EV). |
| You can install an AutoSSL Certificate to secure your informative website or a blog. | If you are running your business, we recommend you to go with a Purchased Certificate as a more robust and trustworthy solution. |

Hosting Australia's Core and higher hosting packages include a free autoSSL certificate. This autoSSL can be found in the SSL/TLS Status section of your cPanel, under the Security heading.
If you see a red padlock, it means your autoSSL is not installed. Simply check the box and run AutoSSL; after a few moments, a pop-up will
appear informing you that your auto-ssl has been installed.
If you have any problems installing autoSSL, try troubleshooting using these methods.
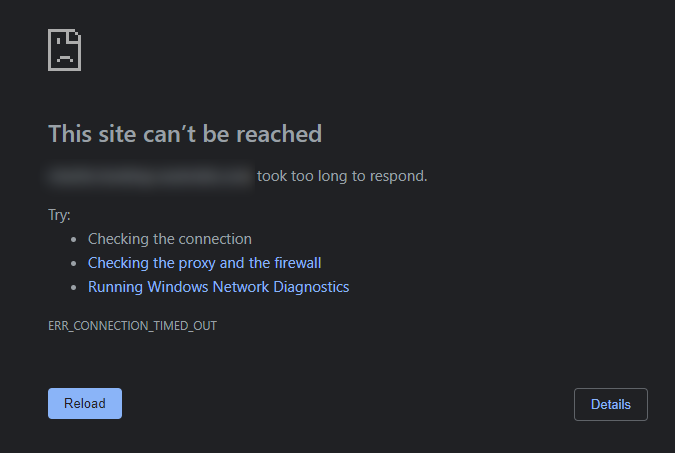
To begin, ensure that your domain is pointed to our nameservers and eventually resolves to Hosting Australia's IP address. Check that your Content Delivery Network (CDN) is properly configured; some CDNs will require you to set up an SSL with them rather than with us. For more information on CDN-related errors, please see the section below. Here are some guides to help you ensure this is correctly configured.
Because your .htaccess file handles rewrite rules and redirects, it is frequently the source of Free SSL problems. .htaccess can be accessed through your File Manager; if you need help locating your File Manager, please see our guide HERE!
Because your plugins can modify the .htaccess file, they frequently cause conflicts. As a test, turn off any security plugins you're using.
When AutoSSL is enabled for an account and a domain or subdomain is added, the server initially generates a Self-Signed request and then works on obtaining an SSL certificate (based on Domain Name Validation).
[/et_pb_text][/et_pb_column][/et_pb_row][/et_pb_section]
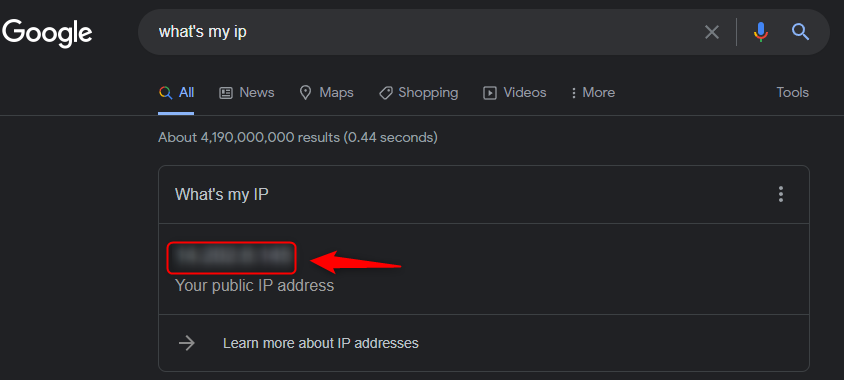
An IP address is a unique number that distinguishes your computer on the internet. An IP address is separated by periods and is expressed as a set of four numbers – an example address might be 192.168.111.25.
Each number in the set can range from 0 to 255. So, the full IP addressing range goes from 0.0.0.0 to 255.255.255.255. Every device connected to the internet has its own IP address, which enables data packets to
be routed along with networks and prevents duplication of addresses.
IP addresses are not generated at random. The Internet Assigned Numbers Authority (IANA), a part of the Internet Corporation for Assigned Names and Numbers, creates, and assigns them mathematically (ICANN). ICANN is a non-profit organisation based in the United States that was founded in 1998 to assist keep the internet secure and accessible to everyone. Every time someone registers a domain name on the internet, they do so through a domain name registrar, who pays ICANN a nominal fee to do so.
Hosting Australia servers have security features in place to protect and prevent themselves from malicious attacks and block the IP address.
An IP blacklist may be caused by the following:
You may have had your IP blacklisted if you are unable to receive emails or access your website. If you believe your IP address has been blacklisted, please contact support at (07) 4914 2433 or via our ticketing system with your IP address so that we can unblock it and investigate why it was blacklisted.
If you need to know our IP address for support, go to whatsmyip.org and it will be displayed at the top of the page, or just Google – What's my IP and it will be displayed at the top of the results.
There are methods you can use to unblock your IP address without contacting Hosting Australia support – You can follow our step-by-step guide HERE!
Hosting Australia's support team will explain why the IP was blacklisted, why it happened, and the best way to resolve the problem. If the IP has been blacklisted because of a failed IMAP login, for example. Support will notify you of the account that is causing the problem and advise you that the account's password must be updated on all devices, or the block will occur again.
Hosting Australia will temporarily whitelist your IP, this prevents your IP from being blocked again while trying to correct the problem devices. If an IP address is whitelisted indefinitely and a device or account is hacked, it would allow the hacker complete control over the server, causing a slew of problems for all accounts and the server's integrity.
So, if you can't access your emails or your website, it's possible that your IP has been blacklisted, and you'll need to contact support to find out why and what you can do to prevent it from occurring again.
Cyber attacks happen every day. They’re a part of the new reality we live in. Advanced hackers use software and technology to infect your computer, steal your information and hold it for ransom. Cybercriminals and cyber terrorists alike are taking advantage of this digital age we live in.
The world is now more connected than ever, with countless ways to get involved online, from paying bills to arranging travel. But those connections also make us more vulnerable, as the bad guys find more ways to make their way into our lives. And they’ve become more brazen as well. In 2016 alone, there were 78 million people who had their personal data breached due to a cyber attack. It's important to know what you should do if you're faced with a similar situation. Here are some reasons why it's essential that you protect yourself by knowing your risk factors and getting educated on the basics of cybersecurity before it happens to you!
A cyber attack is any malicious act that gains unauthorized access to a computer or network with the intent to steal data or disrupt normal operations. This includes everything from a phishing email to a ransomware attack.
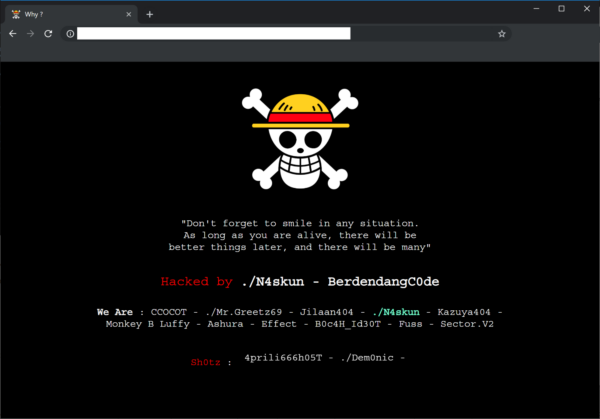
There are a few common warning indicators of a website breach, some of which are more obvious than others:
Viruses, worms, Trojan horses, ransomware, and spyware are examples of malware that can steal your customer data. If Google examines your website and detects anything harmful, it may blacklist your site.
If you have been the victim of a cyberattack, there are a few steps you should take to protect your information and minimize the damage.
First, if you have not been notified by Hosting Australia, you should contact us immediately via our ticketing system or (07) 4914 2433. We will then be able to identify where the attack originated and assist in removing the malicious files and restoring the site.
Make sure all new passwords are what security experts call complex making sure the length (the longer the better), a mix of letters (upper and lower case), numbers, and symbols, no connections to your personal information, and no dictionary words are all important features of a strong password.
If you are struggling to fix a password you can always use sites such as passwordsgenerator.net, random.org, or a password keeper like LastPass, KeePass Password Safe, which enables you to use very strong, complex passwords. No need to remember them — these services do it for you.
Malware is frequently transmitted from one connected device to the next. This is why you should have anti-virus software installed on all of your devices, including tablets and smartphones, such as Bitdefender, Kaspersky, or Malware Bytes. They'll protect your gadgets from incoming threats and notify you if there's a problem. You may buy a license online, and most of them will protect up to five devices.
If you suspect that your customers' data has been compromised, notify them right away. Notify them that there has been a security breach when it occurred, and what information has been compromised. Customers should be encouraged to change their passwords.
The best way to prevent a cyber attack is to educate yourself on the threats. If you know the threats, you will be better equipped to defend yourself. This means understanding your risk factors and getting informed about what different types of cyberattacks look like.
When you receive notifications that an update for your computer or mobile device is available, install it. It's most likely a security patch to keep you safe from a cyber assault. Make sure your website is up to date as well. If it's based on the WordPress platform, for example, make sure to update the WordPress core as well as any plugins you've added on a regular basis to ensure maximum security.
We have noticed there have been more and more phishing emails being sent out recently, If you are unsure about any of these emails DONT click any links. Contact us and forward the email so we can take a look.

Look for a padlock in the browser bar if you're about to fill out an online form with any personal information you'd like to keep private. The website URL will begin with HTTPS if the lock is present. The lock and the HTTPS prefix indicate that the data sent from your browser to the website server is encrypted and secure. Hackers can steal your data if you don't observe these security indications.
As previously said, anti-virus software should be installed on your computer as well as any internet-connected devices, such as tablets and smartphones. We live in a world that is becoming increasingly connected, and one insecure gadget can expose your life to a cyber assault and the theft of your personal information.
When you use any client portal, such as cPanel, banking, social media, you'll almost certainly double-check that you've logged out successfully before continuing your web browsing. However, when it comes to other online accounts, consumers are less cautious, exposing their personal information. So, when you're finished, remember to log out of all of your internet accounts.
If you think you have been the victim of a cyber-attack, the first thing that you should do is to disconnect your computer from the internet. Don't connect it to any other computers on your network. You will need to change all your passwords on every account that you use. This will include your email, bank, social media, and anything else that you log on to.
Once you have done this, find a good internet security suite and install it on every computer in your house. You should also make sure that you have a firewall enabled on your router.
With these safety precautions in place, you will be able to protect yourself from any future cyber-attacks.